Snowden reveals US intelligence’s black budget: $52.6 billion on secret programs
Published 29 Aug, 2013 20:41 | Updated 30 Aug, 2013 18:14
Former intelligence contractor Edward Snowden has leaked a new top-secret document that for the first time ever publically discloses how the United States spends tens of billions of dollars annually on clandestine spy programs.
The Washington Post revealed the so-called “black budget” on Thursday and reports that $52.6 billion was set aside for operations in fiscal year 2013.
Among the biggest priorities for the intelligence community, the Post reported, are “offensive cyber operations” and research devoted to decoding encrypted communications.
The Post’s Barton Gellman, Greg Miller and Julie Tate wrote Thursday that Mr. Snowden, the 30-year-old former Booz Allen Hamilton staffer who started leaking classified national security documents earlier this year, provided the paper with the never-before published summary of this year’s budget.
But although the Post reported that the document is 178 pages in length, they have at the same time elected to only make available one-tenth of the content, citing “concerns about the risk to intelligence sources and methods” brought up by US officials who were notified ahead of publication.
FY 2013 Congressional Budget Justification, provided by Washington Post
“Sensitive details are so pervasive in the documents that the Post is publishing only summary tables and charts online,” the paper wrote in the article that accompanies the 17-page selection. The document is labeled “top secret” and warns that it is only to be accessed by US citizens with the proper security clearance.
Shrouded in secrecy, the amount that Uncle Sam sets aside for sensitive operations each year is not allowed to be published for eyes outside of the intelligence community and only for a portion of those briefed on its operations. The latest Snowden leak reveals that at $52.6 billion, the government is actually handing out 2.3 percent fewer than it did in fiscal year 2012 and, additionally, sequestration has caused the agencies to shed 1,241 positions, or around one percent of its workforce. Despite these setbacks, though, the budget, described by the Post as “a bureaucratic and operational landscape that has never been subject to public scrutiny,” includes billions of dollars towards operations that may not be funded if debated in the press.

In comparison, the Department of Homeland Security was allocated $55.4 billion in FY2013. The black budget comes in at a figure larger than the sums received by the Department of the Interior, the Department of Commerce and NASA this year combined.
Yet despite the hefty cost of operating the secret operations amid sequestration, excerpts from the summary leaked by Snowden show that the US still has significant setbacks keeping it from achieving its intelligence goals.
For one, the disclosure in and of itself demonstrates the intelligence community’s inability to prevent sensitive information from being leaked.
In FY2013, the budget summary says the government invested in ramping-up its counterintelligence operations at a time when budget cuts led to reductions in the community’s workforce, operations, long-term investments, infrastructure and information technology sectors.
“To further safeguard our classified networks, we continue to strengthen insider threat detection capabilities across the community,” the document reads.
As the Post reported, however, the implementation of any insider threat program came too late to catch Snowden, who began mining for documents while employed as a contractor for Dell Inc in May 2012. Snowden began work at Dell in 2009 and it is not immediately clear what security clearance he had before or during the time he started scouring networks for documents, but the Post article claims “a major counterintelligence initiative” budgeted for FY2012 saw its own resources slashed after an “all-hands, emergency response” was ordered to deal with the disclosures then being published by the anti-secrecy group WikiLeaks.
The Post cites an excerpt from this year’s budget where it’s noted that programs are being implemented to “mitigate insider threats by trusted insiders who seek to exploit their authorized access to sensitive information to harm US interests.” Although Snowden’s disclosures — including this one — demonstrate that the $3.64 billion set aside to “integrate counterintelligence” in FY2013 could have likely benefited the intelligence community had it come sooner.
According to one graph included in the document, roughly 39 percent of this year’s black budget was set aside for providing strategic intelligence and warning, with around one-third going towards combating violent extremism. Counter weapons proliferation received 13 percent of total funding, and enhancing cybersecurity and integrating counterintelligence were allotted 8 and 7 percent, respectively.
More broadly speaking, Central Intelligence Agency programs were awarded 28 percent of the total $52.6 billion — or around $14.7 billion, with the Consolidated Cryptologic Program receiving the second most funding with roughly $11 billion. The Post reports that that program includes the National Security Agency on the division of the Air Force, Army, Navy and Marines that involves conducting surveillance and breaking and decrypting codes.
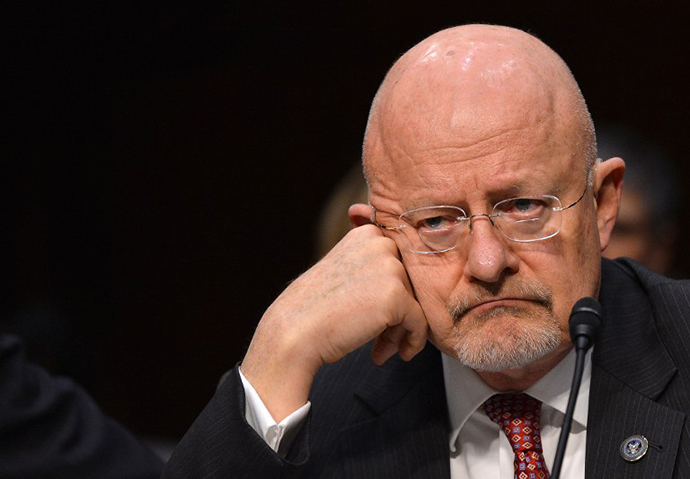
“We are bolstering our support for clandestine SIGINT [signals intelligence] capabilities to collect against high priority targets, including foreign leadership targets,” DNI Clapper says in the summary. “Also, we are investing in groundbreaking cryptanalytic capabilities to defeat adversarial cryptography and exploit Internet traffic.”
Approached by the Post for comment before Thursday’s publication, Clapper said, “The United States has made a considerable investment in the Intelligence Community since the terror attacks of 9/11, a time which includes wars in Iraq and Afghanistan, the Arab Spring, the proliferation of weapons of mass destruction technology, and asymmetric threats in such areas as cyber-warfare.”
“Our budgets are classified as they could provide insight for foreign intelligence services to discern our top national priorities, capabilities and sources and methods that allow us to obtain information to counter threats,” he added.
Through previous disclosures attributed to Snowden, though, the American public has learned that the NSA programs launched to collect foreign intelligence has allowed the federal government to sweep up personal and private information pertaining to Americans who are guaranteed constitution protection from such surveillance.
At the same time, the targeting of foreign persons of interest has apparently suffered significant losses as of late with regards to the intelligence community’s aspirations. The document claims that counterintelligence initiatives are being ramped up against “key targets” including China, Russia, Iran, Israel, Pakistan and Cuba, but the Post reported that five “critical” gaps currently exist keeping the US from collecting as much as it would like on North Korea.
“Analysts know virtually nothing about the intentions of North Korean leader Kim Jong Un,” the Post reported, adding that those critical gaps have given America the inability to properly assess the nuclear and missile programs masterminded from Pyongyang.
Elsewhere, though, the reporters say that other parts of the budget suggest North Korea is anything but an active target.
“A section on North Korea indicates that the United States has all but surrounded the nuclear-armed country with surveillance platforms,” the paper reported. “There are distant ground sensors to monitor seismic activity and scan the country for signs that might point to construction of new nuclear sites. US agencies seek to capture photos, air samples and infrared imagery ‘around the clock.’”

And for those nations of upmost interest, the intelligence community is investing heavily on “offensive cyber operations” launched by the CIA and NSA to hack foreign competitors, steal data and sabotage servers. The Post neglected to publish any excerpts from the summary detailing to what degree the intelligence community has been engaging in these strategic hacks, saying only that recently launched efforts are more “aggressive” than before. As RT has reported extensively in the past, the US government has been accused of being the biggest hackers on the planet at a time when, domestically, so-called cybercriminals are prosecuted at an alarming rate for comparably less harsh crimes.
Last week, RT reported that hacker and political activist Jeremy Hammond of Chicago, Illinois will soon be sentenced for his admitted role in aiding with malicious campaigns targeting the California Statewide Law Enforcement Association, computer servers used by various New York State police chiefs and a company that provides munitions used to gas protesters in Egypt, among others. According to a letter written by Hammond from a New York City jail cell, the US government used a confidential informant within the hacktivist groups Anonymous and LulzSec “to facilitate the hacking of targets of the government’s choosing – including numerous websites belonging to foreign governments.”
“Why was the United States using us to infiltrate the private networks of foreign governments? What are they doing with the information we stole? And will anyone in our government ever be held accountable for these crimes?” Hammond asked.












