Decrypt or else: Draft encryption bill says tech companies must comply with court orders
Published 8 Apr, 2016 20:30
A leaked draft of a Senate bill addressing the fight between Apple and the FBI over encrypted data on an iPhone indicates lawmakers are pursuing a strict policy that would require compliance with court orders and a possible ban on end-to-end encryption.
A draft of the encryption bill, being crafted by Senators Dianne Feinstein (D-California) and Richard Burr (R-North Carolina), was leaked to The Hill newspaper, revealing that the top members of the Senate Select Committee on Intelligence want any company that provides data or communications services to "provide, in a timely manner, responsive, intelligible information or data, or appropriate technical assistance to obtain such information or data," if ordered to do so by a court.
The data must be offered to the government in an “intelligible format if such data has been made unintelligible by a feature, product or service owned, controlled, created or provided by the covered entity or by a third party on behalf of the covered entity," says the draft legislation, also known as the Compliance with Court Orders Act of 2016.
On its face, the Feinstein-Burr bill isn't just limited to law enforcement/intel--any court order, even civil, would qualify! Gee whiz.
— Kevin Bankston (@KevinBankston) April 8, 2016
"Intelligible" is defined in the draft as “decrypted, deciphered, decoded, demodulated, or deobfuscated to its original form.” Though it does not explicitly mandate design changes to products, the draft does go on to prohibit any features, such as end-to-end encryption, that would impede a company from complying with a court order. For example, Whatsapp, a messaging service with end-to-end encryption, would not be able to follow such a court order without modifying its system.
“This basically outlaws end-to-end encryption,” Joseph Lorenzo Hall, chief technologist at the Center for Democracy and Technology, told Wired. “It’s effectively the most anti-crypto bill of all anti-crypto bills.”
I could spend all night listing the various ways that Feinstein-Burr is flawed & dangerous. But let's just say, "in every way possible."
— matt blaze (@mattblaze) April 8, 2016
Companies warned that allowing backdoors will make users vulnerable to far more than government investigations.
“The truth is backdoors would be accessible to more than just the government. We don’t need to help criminals and hackers steal our data,” said Dave Wagner, CEO of email encryption provider ZixCorp, according to International Business Times.
The anti-encryption bill from Senators Burr & Feinstein would be disastrous for #cybersecurity and the tech economy. https://t.co/W9V4eiXoYy
— Open Tech Institute (@OTI) April 8, 2016
The senators responded by saying that the leaked version of the legislation is only a draft, but that a court order should be final in such cases.
"[W]e’re still working on finalizing a discussion draft and as a result can’t comment on language in specific versions of the bill," Tom Mentzer, a spokesman for Feinstein, told Wired in a statement.
"However, the underlying goal is simple: when there’s a court order to render technical assistance to law enforcement or provide decrypted information, that court order is carried out. No individual or company is above the law. We’re still in the process of soliciting input from stakeholders and hope to have final language ready soon.”
Am I right that the Feinstein-Burr decryption bill just kinda forgets to say anything about remedies for violations? https://t.co/uJMX78MWUV
— Orin Kerr (@OrinKerr) April 8, 2016
Just prior to the leak of the draft bill, Reuters reported that the White House is not offering public support to the legislation in its current form and remains divided on the issue.
It's not hard to see why the White House declined to endorse Feinstein-Burr. They took a complex issue, arrived at the most naive solution.
— Matthew Green (@matthew_d_green) April 8, 2016
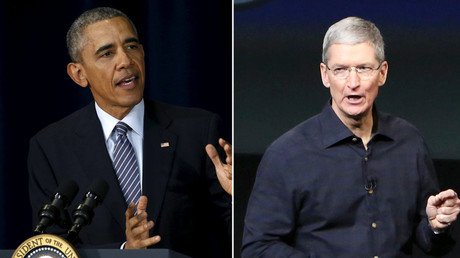
The bill is a response to the battle between Apple and the Department of Justice over the latter's desire to thwart encryption features of an Apple iPhone 5C owned by Syed Farook, one of two shooters who killed 14 people in San Bernardino, California, in December. Apple refused to comply with a court order requiring it to assist the FBI in creating a backdoor to the phone. A high-profile legal battle ensued, with Apple saying the request would set a "dangerous" precedent for digital privacy, and that such a key "could be used over and over again, on any number of devices."
Without confirming Burr/Feinstein wrote leaked draft, Sen. Wyden tells me it's concerning: https://t.co/IZlubRz4JLpic.twitter.com/gZp9RLrgHK
— Jenna McLaughlin (@JennaMC_Laugh) April 8, 2016
Google, Facebook, Snapchat, Amazon, Microsoft and Twitter all filed legal briefs in support of Apple's position in its court case with the FBI. Other tech companies, including LinkedIn and Reddit, offered a separate court filing in support of Apple, saying that an undermining of iPhone security "threatens the core principles of privacy, security, and transparency that underlie the fabric of the Internet."
Just as the two parties were scheduled to go to court late last month, a federal judge agreed to the FBI’s request to postpone the hearing, after prosecutors announced that an unnamed "non-governmental third party" had presented a potential way to crack Apple’s flagship product without the company’s help. That third party is reportedly Cellebrite, an Israeli mobile forensic software company.
On Wednesday, FBI Director James Comey revealed the agency’s methods for cracking Apple encryption to Feinstein and Burr.
“I don’t believe the government has any obligation to Apple,” Feinstein told the National Journal. “No company or individual is above the law, and I’m dismayed that anyone would refuse to help the government in a major terrorism investigation.”