FBI using Israeli firm to crack San Bernardino iPhone without Apple
Published 23 Mar, 2016 20:13
Cellebrite, an Israeli mobile forensic software company, is aiding the Federal Bureau of Investigation in its quest to unlock the iPhone used by one of the San Bernardino shooters, Israeli media reported.
Cellebrite, an Israeli mobile forensic software company, is aiding the Federal Bureau of Investigation in its quest to unlock the iPhone used by one of the San Bernardino shooters, Israeli media reported.
The FBI has been contracting with Cellebrite to break through a locked iPhone, “according to experts in the field familiar with the case,” according to Ynet, online outlet of the Israeli newspaper Yedioth Ahronot.
This would be a step in a much different direction in the FBI’s ongoing battle with Apple over the device belonging to Syed Farook, one of the perpetrators of December’s massacre in San Bernardino, California, that left 14 people dead.
Cellebrite, considered a global leader in the field of digital forensics, hasn’t officially commented on their involvement with the FBI. However, The Verge reported the company has had a sole-source contract with the Bureau since the 2013, specifically to help with data extraction – the very task at hand in the San Bernardino case.
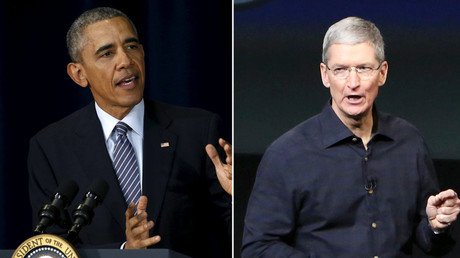
The FBI initially attempted to force Apple to crack the iPhone via an ongoing court battle, one which the company’s CEO Tim Cook said he was willing to carry all the way to Supreme Court, to defend the privacy of its customers.
Just as the two parties were scheduled to go to court on Tuesday, a federal judge agreed to the FBI’s request to postpone the hearing, after prosecutors announced that an unnamed "non-governmental third party" had presented a potential way to crack Apple’s flagship product without the company’s help.
If the third party successfully bypasses the iPhone’s security features, it could have business implications for Apple that go beyond this particular case.
Other tech giants – and as of this month, the Department of Defense – routinely set bounties for identifying and fixing exploitable flaws for outside hackers to claim. Facebook paid out almost $1 million total in such bounties to independent researchers who found bugs in 2015, and Google paid hackers $6 million in 2010.
Apple, however, doesn’t engage in this industry-standard practice, and hackers have turned to underground markets to sell knowledge of flaws in the company’s software that not even the company itself has, and this could be why the FBI is able to turn to third parties.
The showdown between Apple and the federal government has spilled over from the realm of the courts and technology, finding itself under the scrutiny of lawmakers. Senators Dianne Feinstein (D-California) and Richard Burr (R-North Carolina) have been working since the Paris terror attacks in November, followed quickly by the one in San Bernardino, on an encryption bill that could be introduced to the Senate any day, reported The Hill.
Feinstein and Burr argue that it is currently too easy for criminals and terrorists to “go dark,” and the new bill would force companies like Apple to comply with court orders that seek access to encrypted communications.
“The going-dark issue has been gathering momentum (in Congress) like a train coming down the tracks, but it still seemed for a while like it was going to be a long time before it got to the station,” said Representative Adam Schiff, the top Democrat on the House Intelligence Committee, according to Reuters. “But it arrived with a fury with this lawsuit.”