Revealed: Electronic voting system hacked in DC
Published 14 Mar, 2012 21:07 | Updated 15 Mar, 2012 01:13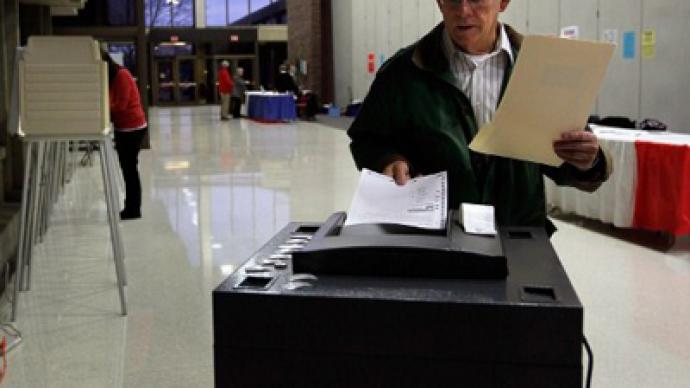
When Washington, DC decided to try out an Internet voting system to make casting absentee ballots as easy as clicking a mouse, they dared hackers to compromise the contest. It was a feat accomplished in less than two days.
The District of Columbia hosted a public trial before going live with an e-voting program to see if their presumably impenetrable online ballot system could sustain a cyber attack. If you’re wondering why they never followed through, it is because the government is going to need a lot more time with this one. “Within 48 hours of the system going live, we had gained near complete control of the election server," researchers from the University of Michigan explain in a write-up of their 2010 hack of an e-voting system that DC was debating on pushing live. They managed to gain access and make massive alterations to the internal configuration of the voting site in two years, write the researchers, who presented their work at a cryptography and data security conference in the Caribbean last month. With elections regularly plagued with allegations of inaccuracy and fraud, jurisdictions across the country have debated since the dawn of the Information Age if democracy would translate well to the Web. Although logging-on to pick a future president might someday be an option that is a lot easier than driving to the nearest polling place, the report out of the University of Michigan suggests that there is a ways to go before that goal is reached.Not only did the team of researchers manage to expose the would-be voting system as one with rather lax security, they also explain in their findings that is was rather easy to do devastation once inside the system. “We successfully changed every vote and revealed almost every secret ballot,” writes the researchers — Scott Wolchok , Eric Wustrow, Dawn Isabel and J. Alex Halderman — adding that Election officials did not detect their intrusion for at least two days, “and might have remained unaware for far longer had we not deliberately left a prominent clue.”The severity of what they accomplished, they write, was something they also felt that DC would be unable to bounce right back from. “Recovery from this attack is difficult; there is little hope for protecting future ballots from this level of compromise, since the code that processes the ballots is itself suspect,” reads their report.“This case study — the first (to our knowledge) to analyze the security of a government Internet voting system from the perspective of an attacker in a realistic pre-election deployment — attempts to illuminate the practical challenges of securing online voting as practiced today by a growing number of jurisdictions."The group goes on to say that they wanted to not necessarily take advantage of the open invite from Washington to test their abilities, but to act as accurately as actual hackers would. “Our objective was to approach the system as real attackers would: starting from publicly available information, we looked for weaknesses that would allow us to seize control, unmask secret ballots and alter the outcome of the mock election,” they write. After the hack was first revealed, Paul Stenbjorn of the DC Board of Elections and Ethics bluntly admitted, “The integrity of the system had been violated” and said that, upon analyzing the footprints left by the researchers, “they had to be able to change anything they wanted on the Web site.”Even two years after they admitted to their attack, security is still considered largely under par as far as government entity’s online presence is concerned. The FBI recently called cyberattacks the biggest threat facing America and officials from within NASA admitted that the United States department that overseas billions worth of high-tech gadgetry is not only highly susceptible to hacks — but is also regularly attacked.