MI5 warns businesses foreign spies targeting their IT staff - report
Published 6 May, 2014 09:06 | Updated 27 Jun, 2014 08:12
MI5, the British intelligence agency, has reportedly warned that foreign agents are attempting to recruit IT corporate employees – even low-level contractors – to gain access to classified data.
In these post-Snowden times, when all electronic information and
communication has been proven vulnerable to some form of spying,
UK intelligence is warning corporate executives in
“high-level conversations” on the importance of boosting
their “digital defenses,” the Financial Times reported, quoting anonymous Whitehall
officials.
The warning comes as the government works to beef up digital
security at important institutions such as “banks, utility
companies or energy providers,” some of which remain
vulnerable to espionage.
According to the UK’s national security risk assessment,
cyber-attacks rank as a “tier 1 threat,” which is
defined as an event that is both likely to occur and to have a
major impact.
While most businesses and government agencies now understand the
importance of protecting their data from external infiltration
via the internet, less attention is being given to internal
espionage being carried out by their own employees.
“Grooming a source with access to highly sensitive
information used to be a process that Cold War spymasters would
spend years orchestrating,” the FT said. Today, however,
“even the most junior IT employees can be highly coveted
intelligence assets thanks to their often wide-ranging network
privileges.”
“IT department employees have been recruited to help foreign
spies gain sensitive personnel information, steal corporate or
national secrets and upload malware to compromise entire
networks, security officials believe.”
With the intensification of computer technologies and their
applications, it is easy to forget the ‘human side’ of espionage,
which did not disappear together with the Cold War.
Indeed, in some cases it resembles the high-octane adventures of
a James Bond thriller.
As London-Moscow relations turn chilly over the deteriorating
situation in Ukraine, MI5 last month warned British diplomats not to fall victim
to so-called “honey traps,” that is, relations with
foreign femme fatales who possess the equivalent of a black belt
in beauty and the art of seduction.
In 2009, for example, a British diplomat was forced to quit the
Foreign Office after he was filmed in the company of two women at
a massage parlor in Russia.
However, British spies have also been known to employ a few
dastardly tricks of their own in a trade that is nearly as old as
soliciting sex.
In 2006, the FSB, Russia’s intelligence service, exposed a
high-tech “spy rock” that was positioned alongside a
Moscow street that enabled British agents to relay information in
a modern version of a “dead-letter drop.”
In any case, governments around the world are now working to
protect their secrets like never before.
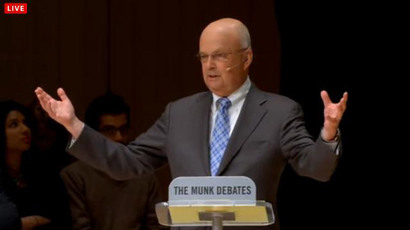
“Insider threats are the growing challenge,” Paul
Stockton, the former US assistant secretary of defense, who is
now managing director of risk-management company Sonecon, told
the FT. “The threat of espionage did not end with the Cold
War.”
Stockton appeared to be specifically addressing the type of
threat presented by a relatively low-level security contractor
such as Edward Snowden, who last year blew the whistle on the
global surveillance work of the National Security Agency (NSA) –
even though Snowden acted of his own volition.
“The highest risk employees, they’re not necessarily those at
the highest levels of an organization who in the old days would
have had access to the very limited number of paper documents
that would have been most attractive to a foreign power,”
Stockton said. “Rather it is systems administrators and
others who hold the keys to the IT kingdom that pose such
significant potential threats.”
In July, at the height of the Snowden scandal, an order placed by
Russia’s Federal Guard Service (FSO) for 20 typewriters triggered media speculation that the move was
in response to the NSA revelations.
However, an FSO source told RT that Russian special services have
always used typewriters, saying that it was simply time to
replace the old equipment.
“It’s not something unusual...the time came to change them.
Everyone has these typewriters – the Emergencies Ministry,
Ministry of Defense, every special service has them,” the
source said.