NASA loses laptop with command code for ISS
Published 1 Mar, 2012 23:22 | Updated 2 Mar, 2012 20:37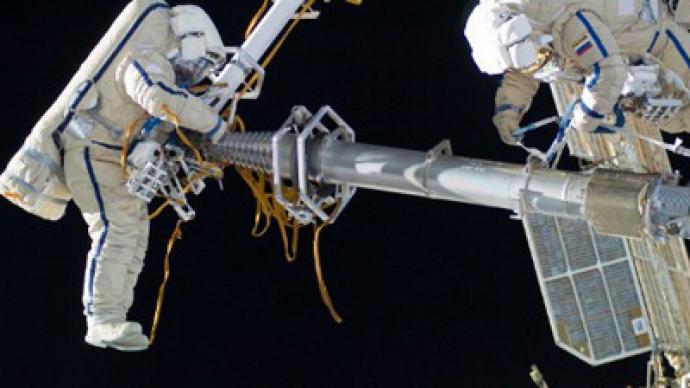
Four dozen high-tech computing devices disappeared from the offices of NASA over a two-year span, including one laptop that contained the code needed to command the International Space Station.
No big deal, guys!A laptop with the algorithm used to control the ISS was one of 48 gizmos and gadgets that NASA either reported lost or stolen between April 2009 and April 2011, the agency’s inspector general, Paul Martin, tells the House Committee on Science, Space and Technology. Although the incidents date back to nearly three years ago, Martin has only now informed Congress of the accidents. They are discussed in a written statement he authored and published this week under the title “NASA Cybersecurity: An Examination of the Agency’s Information Security.”For the Cliff Notes version, we’ve got you covered. Information security at NASA: not so good. Over the course of ten pages, Martin makes mention of what he says are five issues that NASA believes, based on their “extensive audit and investigative work,” make up NASA’s “most serious challenges in the admittedly difficult task of protecting the agency’s information.”For starters, we suggest putting a damn lock on the safe.Martin goes on to list those challenges as including a “lack of full awareness of Agency-wide security posture,”“shortcomings in implementing a continuous monitoring approach to IT security” and the “slow pace of encryption.” Also, however, he adds that one “challenge” in particular, is the ability to handle a sophisticated cyber attack. Now, what separates a sophisticated cyber attack from a stupid, simple-minded one is something Martin would have to extrapolate on a bit more. But in regards to losing four dozen mobile computing devices — well, keeping a close eye on those things isn’t rocket science. And if it was, you’d expect NASA of all agencies to be able to handle it, wouldn’t you?According to the congressional testimony, NASA spends around $1.5 billion each year on IT-related activities, which includes approximately $58 million on IT security. And while the statement acknowledges that losing sensitive information could “adversely affect national security,” Martin makes note that lapses have caused concern time and time again. He also admits that security within the agency is not up to snuff, while at the same time revealing that NASA is a “regular target” of such attacks. The 48 missing mobile devices isn’t the biggest number in the report, though. In 2010 and 2011, reveals the report, NASA reported over 5,400 incidents where either malicious software was found on computers or unauthorized users were granted access to the agency’s systems. For the sake of pointing out the significance of how spectacular of a security flaw this is, we will publish this line as a standalone statement:NASA SUFFERS OVER 5,000 SECURITY BREACHES A YEAR ON A SYSTEM THAT IS IN CHARGE OF GIANT, SPACE-SURFING MISSILES.You would only assume that if they can land a man on the moon, surely they could install a copy of McAfee Antivirus.Those problems, adds the report, have indeed caused the disruption of mission operations and is estimated to have costs NASA $7 million in just one years’ time. In their defense, however, the agency has issued 21 audit reports during the last five years, which have spawned 69 IT-related recommendations. Whether or not they followed through with those, however, is anyone’s guess. Regardless, Martin does make note that the agency has identified that there is indeed “weakness” in regardless to its IT security. That, you see, is something you shouldn’t have to admit to. Over the span of just ten pages, the word “weakness” appears four times.One of those weaknesses is indeed the ability to monitor mobile devices that are lost. The damage, reveals the report, has been not just the loss of the code used to command and control the International Space Station (that one-million-pound hunk of machinery that NASA allocated $72.4 billion towards), but also Social Security numbers and other sensitive data. Don’t worry too hard, though. NASA says that eventually they will able to remediate these issues. It’ll take a bit of work though. "Until NASA fully implements an agency-wide data encryption solution, sensitive data on its mobile computing and portable data storage devices will remain at high risk for loss or theft," reads Martin’s report.And if you were wondering, “risk” appears an average of twice-per-page in the report.












