Lavabit appeals government order to divulge its private keys
Published 11 Oct, 2013 04:04 | Updated 11 Oct, 2013 04:08
Lavabit, the secure email provider used by NSA whistleblower Edward Snowden, has filed its first brief in what is considered a landmark privacy case, revealing more details of its resisting an aggressive government investigation.
The email provider’s founder, Ladar Levison, shut down rather than comply with a government order issued July 16 to release its private SSL keys, or rather the keys to its encryption, which would have left the service’s 40,000 users exposed as authorities poured through data for any useful evidence on Snowden.
According to a brief filed in the 4th US Circuit Court of Appeals Levison is appealing that court order, and a government response will be due by November 4th.
In that document Lavabit outlines its position, defending its refusal to hand over private keys as they “were not contraband, were not the fruits of any crime, were not used to commit any crime, and were not evidence of any crime.”
The 44-page document argues that the pen register statute--legislation originally focused on telephony but now routinely used to extract electronic data--does not authorize the US government to seize the email service's keys, nor does the Stored Communications Act.
Lavabit's appeal further states that the Fourth Amendment forbids the seizure of its SSL keys, and protects against the access of its customers' data.
“The Fourth Amendment insists that a warrant name particular things to be searched; a warrant that permits open-ended rummaging through all of Lavabit's communications data is simply a modern-day writ of assistance, the sort of general warrant that the Fourth Amendment was ratified to forbid."
The email service points out that officials forbade Lavabit from informing anyone, including its customers and partners, that it had compromised its security. According to the brief, government officials "insisted that all of those parties be affirmatively misled into believing that the system remained secure against exactly the kind of secret monitoring that the government was proposing."
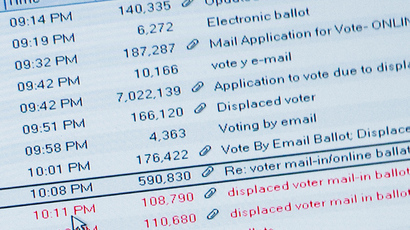
Interestingly, Lavabit also details that it had proposed a compromise in turning over the target's (in this case almost certainly Edward Snowden) "login and subsequent logout date and time, the IP address used to connect" along with what it describes as "non-content headers" from any future emails sent or received by the subject's account.
That offer was refused, as authorities instead demanded that they be given “real time” access to their target customer’s data.
Lavabit’s offer does, however, seem to undermine the notion that officials would have required access to all of the email client’s data to sift through and determine which portion was pertinent to its investigation.