US-Israeli computer super-worm hit Russian nuclear plant - Kaspersky
Published 12 Nov, 2013 17:30 | Updated 12 Nov, 2013 19:50
The CEO of one of the world’s foremost computer security firms says the Stuxnet worm that targeted Iranian nuclear facilities may have also infiltrated similar critical systems in Russia.
If accurate, allegations that Stuxnet snuck its way into Russia could implicate the United States and Israel in an even broader act of cyberwar than previously reported.
Since Stuxnet was discovered in 2010, the media has all but confirmed that the US and Israel collaborated on the computer worm to try and cripple machinery inside Iran’s nuclear power plants. Senior White House officials speaking to the New York Times have previously lent credence to that accusation, National Security Agency whistleblower Edward Snowden confirmed in a Der Spiegel interview earlier this year and the origin of the worm is nowadays hardly contested. Speaking in Australia last week, however, the head of the international IT firm, Kaspersky Lab, raised new questions regarding the actual scope of the secretive program.
Eugene Kaspersky was making a presentation at the National Press
Club of Australia on the topic of cybersecurity when he warned of
the serious ramifications that could be caused by unleashing
viruses.
According to the computer scientist, he received a message a few years ago from a friend who worked at a Russian nuclear power plant in which the source claimed “their internet network [was] badly infected by Stuxnet.”
The facility in question, Kaspersky added, is not wired to the Internet, suggesting that Stuxnet may have hopped its way onto an air-gapped system after being manually brought into the Russian nuke plant, such as on a portable drive.
Kaspersky didn’t point the finger at any parties in particular, but said, “Unfortunately, these people who are responsible for offensive technologies recognize cyber weapons as an opportunity.”
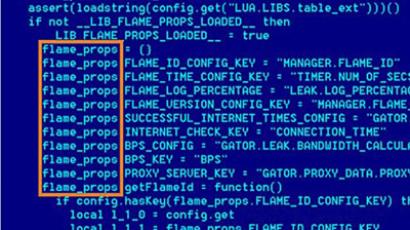
Security expert, Graham Cluley, wrote about the Stuxnet worm on his website this week and acknowledged, "Indeed, the very fact that it spread out of control, was what lead to its discovery by security firms." But while companies like Kaspersky and Symantec have made great headway in tracking down the origin of Stuxnet and its sister worms, Flame and Gauss, revelations like the one last year in which Chevron claimed to have been infected by the same piece of malware has already suggested that the virus’s authors may have caused more collateral damage than they had bargained for.
With regards to the latest claims about the Russian plant, serious fallout could occur between major world powers if Kaspersky’s claim is correct and the disconnected nuclear system there really was infected by the Stuxnet worm.
"If the claim of the Russian nuclear plant infection is true, then it's easy to imagine how this ‘collateral damage’ could have turned into a very serious incident indeed, with obvious diplomatic repercussions,” Cluley added.
After Kaspersky’s remarks began to circulate like wildfire on the Web, his company issued a press release reiterating the size and scope of Stuxnet, based on what scientists have already managed to learn.
“According to data from the Kaspersky Security Network, by the end of September 2010, more than 100,000 computer systems in approximately 30,000 organizations around the world were infected by Stuxnet,” the company confirmed.
As Kaspersky told the crowd in Australia, though, these computer worms — estimated to cost tens of millions of dollars to manufacture — are indeed quite capable of coming back and infecting entities it never intended to impact.
“Everything you do is a boomerang. It will get back to you,” he said.
According to Kaspersky, companies need to take necessary steps to protect themselves from hackers, whom he estimates to be behind millions of attacks every day. And even if attacks against critical infrastructure components are limited, he cautioned that no target is was too large to be subject to a cyber-attack.
“The space guys from time-to-time are coming with USBs, which are infected,” Kaspersky said. “ I'm not kidding. I was talking to Russian space guys and they said, 'yeah, from time-to-time there are viruses on the space station.”
"So these computer networks are everywhere around," he said, "and unfortunately they are not safe by design."
However, major Russian nuclear authority Rosatom has denied
allegations that its plant was ever affected by the Stuxnet worm.