Flame and Stuxnet: Two cyber weapons unleashed by same master
Published 11 Jun, 2012 22:26 | Updated 12 Jun, 2012 03:26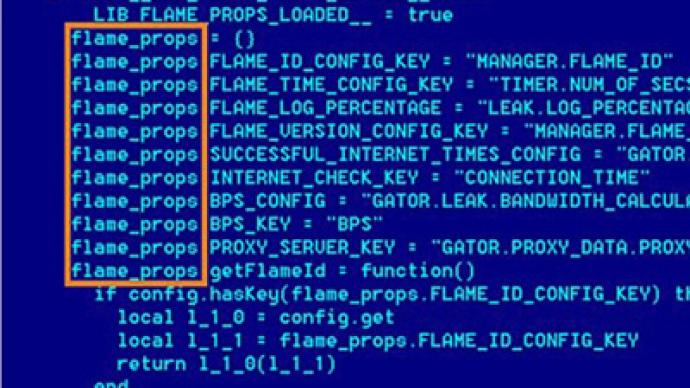
Those who commissioned the malware Flame also created the deadly Stuxnet, say Kaspersky Labs, who have discovered an identical piece of code in both worms. What appeared to be two unrelated programs are probably part of the same cyberwar campaign.
"The new findings that reveal how the teams shared the source code of at least one module in the early stages of development prove that the groups co-operated at least once," wrote Aleksandr Gostev, chief security expert for Russian security company Kaspersky Labs.Flame, which was discovered only last month, despite operating for several years, is a cyber-espionage program. After infiltrating computer systems through hundreds of possible vulnerabilities, it records all of the user’s information, from printed documents to voices recorded on the microphone.In contrast, Stuxnet is a weapon. In 2010 it was used to damage uranium enrichment centrifuges in Iran.In fact, Iran was by far the most popular destination for both of the targeted worms, which experts deemed the most sophisticated ever discovered.Kaspersky Labs believes the two worms were developed by independent groups controlled by the same party."We think that these teams are different, two different teams working with each other, helping each other at different stages," said Vitaliy Kamluk, the company’s chief malware expert.It is possible that the two programs were always intended to work together. The earlier Flame may have been used to spy on targets, and Stuxnet to decimate them.The United States and Israel have been widely fingered in the media and by officials as the makers of Stuxnet, and will now likely be associated with Flame as well.The two countries both vehemently oppose Iran’s nuclear program, which they believe is aimed at eventually acquiring nuclear weapons.Considering the lag of several years between their introduction and the discovery of the programs, analysts believe that even more advanced cyber weapons may currently be in operation.
















