'Nothing to bypass': Ashley Madison security is awful, hackers say
Published 22 Aug, 2015 03:50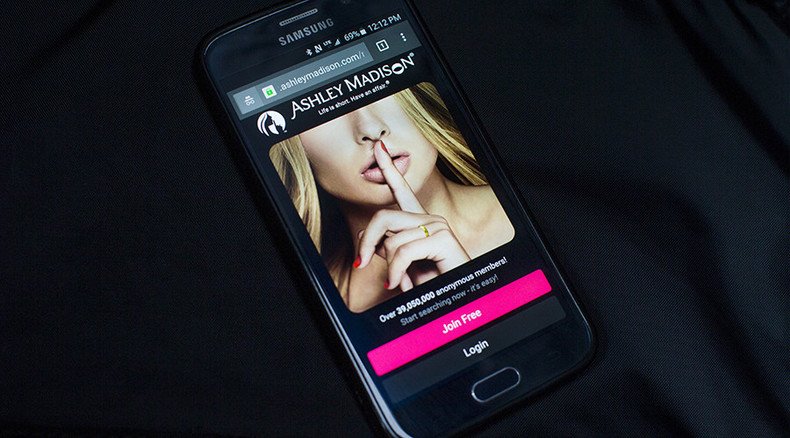
The hackers behind the embarrassing Ashley Madison data dumps have finally broken their silence, claiming in an interview that the website had “no security” and was extremely easy to sneak into.
If true, the news would be extremely embarrassing for an infidelity service that explicitly boasts about the number of “anonymous” members it has. The website also claims on its front page that it is “100 percent discreet” and has a “Trusted Security Award.”
In an interview with Vice’s Motherboard, the hackers who call themselves the “Impact Team” called themselves “very experienced” and said that while they prepared a security breach that would have made their attack “fully undetectable,” they found “nothing to bypass” when they broke into Ashley Madison.
“Nobody was watching. No security. Only thing was segmented network,” the team said in a Q&A.
The team said it collected about 300 gigabytes of employee emails and documents. Additionally, they said they gathered “tens of thousands” of user pictures, about 33 percent of which were pictures of members’ penises (they will not be released, the hackers said).
#AshleyMadison hackers dump fresh data trove online, taunt founder
http://t.co/sIb4eZOacQpic.twitter.com/SA8Mk8nXx5
— RT America (@RT_America) August 21, 2015Despite claiming that members would have their privacy protected, Ashley Madison’s privacy policy states that it could not guarantee this data would be protected.
"You acknowledge that although we strive to maintain the necessary safeguards to protect your personal data, we cannot ensure the security or privacy of information you provide through the Internet and your email messages,” the policy read, according to CNN.
Asked to react to fact that Ashley Madison remained online even though the Impact Team threatened to release troves of member data, the hackers said they weren’t surprised because “They make $100,000,000 in fraud a year,” going on to say that the site claims not to store credit card information even though their processors store numbers and billing addresses.
On Tuesday, the hackers released approximately 10 gigabytes of member data, including names, emails, and descriptions of sexual desires they hoped to fulfill through the service. Ashley Madison attempted to raise doubts about the leak’s authenticity, but another 20 gigabytes of internal data was released Thursday with a message to the site’s founder.
“Hey Noel, you can admit it’s real now,” the message said, likely referring to Noel Biderman, the CEO of Avid life Media, the parent company of Ashley Madison.
Thousands of government emails implicated in #AshleyMadison affair #ashleymadisonhack
http://t.co/qDe2Kjy9Zdpic.twitter.com/kAFzmq9HNy
— RT America (@RT_America) August 19, 2015Meanwhile, media reports have stated that hundreds of government and military officials may be implicated in the leak. The Defense Department announced Thursday that it will be investigating the use of Pentagon emails to see if military service members had used the service, since adultery is punishable under military law.
“I’m aware of it,” Defense Secretary Ashton Carter said of the issue. “Of course it’s an issue because conduct is very important. We expect good conduct on the part of our people. The services are looking into it, as well they should be, absolutely.”
Notably, the Impact Team told Motherboard that more info may be on the way – from companies other than Ashley Madison.
“Any companies that make 100s of millions profiting off pain of others, secrets, and lies. Maybe corrupt politicians,” they said. “If we do, it will be a long time, but it will be total.”













