Thousands of government emails implicated in Ashley Madison affair
Published 19 Aug, 2015 22:18 | Updated 20 Aug, 2015 14:50
The release of records pilfered by hackers from the infidelity website Ashley Madison may present a headache for thousands of US government and military personnel, who used their official emails to register.
According to preliminary analysis of the data, which appeared on the 'dark web' on Tuesday, almost 60,000 members have addresses in Washington, DC, and over 15,000 accounts were affiliated with a .gov or a .mil address.
After holding the data hostage for a month, the hacker group calling itself Impact Team released almost 10 gigabytes of Ashley Madison records, containing sensitive customer information such as payment transaction and credit card details, emails, names, addresses, phone numbers and member profiles.
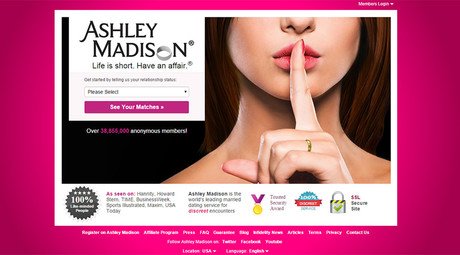
Owned by Avid Life Media, Ashley Madison boasts over 38 million users drawn to the company’s slogan “Life is short. Have an affair.” Membership is free for women, while men pay $49 for 100 credits on the site, used to chat, send messages and virtual gifts.
Hackers release data of millions of #AshleyMadison cheating site users http://t.co/29CJRDIpOCpic.twitter.com/yZ9HEfXyEt
— RT America (@RT_America) August 19, 2015As the website DCist pointed out, the leaked records list 15,019 accounts using an email address belonging to domains used by the US government or the military. Some 6,788 accounts used us.army.mil emails, while the Navy and the Marines accounted for 1,665 and 809, respectively.
A list compiled by one Twitter user gives a detailed breakdown of all the emails from government domains included in the data dump.
The government agency with the most Ashley Madison users – 104 – was the already scandal-ridden Department of Veterans Affairs (va.gov). Federal Bureau of Prisons had 88 email addresses, 52 belonged to the US Postal Service, and 45 to the Department of Homeland Security.
Employees of the Social Security Administration (42 emails), the State Department (33) and the IRS (six) were also on the list. Local government employees in the District of Columbia (22) and Montgomery County, Maryland (22 as well) also used work addresses to sign up for extramarital affairs.
According to the data dump, there are 44 accounts using a WhiteHouse.gov email address. However, White House officials actually use a different domain, eop.gov, noted The Hill.
Since Ashley Madison did not require email verification, anyone could have used addresses from government domains or made-up ones. However, users of the site may still be identified by other data included in the release.
“It appears to contain addresses, as well as GPS coordinates. I suspect that many people created fake accounts, but with an app that reported their real GPS coordinates,”wrote Robert Graham, CEO of Errata Security, adding that the data in the dump “appears legit.”
US officials caught looking for #sex at #AdultFriendFinder website from govt email accounts http://t.co/H053G2itnPpic.twitter.com/MXaQrBp7zL
— RT (@RT_com) May 22, 2015This would not be the first time government employees have used work emails to register for shady online services. In May 2015, hackers leaked personal information of approximately 3.9 million users of Adult Friend Finder, including online handles, email addresses and sexual preferences. Among the public officials caught with their pants down were employees of the Department of Homeland Security, Federal Aviation Administration, and the Washington, DC police.