Lawmakers look to reform anti-hacking law by reintroducing bill for Aaron Swartz
Published 22 Apr, 2015 18:42 | Updated 22 Apr, 2015 18:42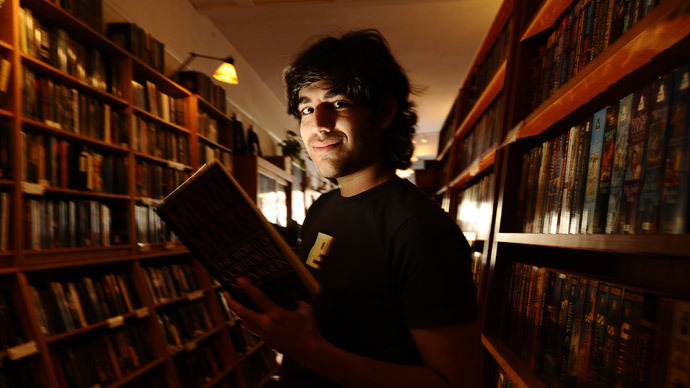
Legislation named in honor of the late activist Aaron Swartz aimed at fixing a 30-year-old anti-hacking law has been brought back to Capitol Hill after stalling during the last congressional session.
A proposed update to the federal Computer Fraud and Abuse Act, or CFAA, would introduce reform “to better target serious criminals and curb overzealous prosecutions for non-malicious computer and Internet offenses,” according to its authors. So far, their offering has already garnered bipartisan support in both the House and Senate.
Reintroduced Aaron’s Law today with @RepZoeLofgren & @RandPaul. We must stop this prosecutorial malpractice http://t.co/Lboq2mz5dV
— Ron Wyden (@RonWyden) April 21, 2015
Senators Ron Wyden (D-Oregon) and Rep. Zoe Lofgren (D-California) had previously introduced the bill to Congress shortly after Swartz committed suicide in January 2013 at the age of 26. Federal prosecutors in the District of Massachusetts had charged the renowned activist and programmer with violating the CFAA in 2011 after Swartz had allegedly downloaded millions of scholarly articles from an academic research database. He stood to face a maximum sentence of 35 years in prison and a $1 million fine, if he was found guilty. Swartz ultimately hanged himself in a New York apartment three months before his trial was scheduled to begin.
Removing the redundancies, defining authorization
Wyden and Lofgren say that the implementation of Aaron’s Law would clarify the CFAA’s language in order to better define what constitutes unlawful access to a computer system, while also eliminating verbiage they believe to be redundant and penalties they call disproportionate.
"The Computer Fraud and Abuse Act is long overdue for reform," Lofgren said in a statement this week. "At its very core, CFAA is an anti-hacking law. Unfortunately, over time we have seen prosecutors broadening the intent of the act, handing out inordinately severe criminal penalties for less-than-serious violations. It's time we reformed this law to better focus on truly malicious hackers and bad actors, and away from common computer and internet activities."
Previously, Lofgren and Wyden said the goal of Aaron’s Law was to bring balance to the CFAA, by eliminating language that can allow a suspect to be charged more than once for the same violation. Speaking to Wired in 2013, the lawmakers said of Swartz’s case that “more than a third of the charges in the superseding indictment against him were under this redundant CFAA provision,” and that “Eliminating the redundant provision streamlines the law, reduces duplicative charges but would not create a gap in protection against hackers.”
The CFAA made headlines again last year when a 27-year-old Texas man, Fidel Salinas, was charged with 44 counts related to suspicious computer activity and faced upwards of 440 years in prison before he pleaded guilty to a misdemeanor. In a statement, the author's of Aaron’s Law’s said their proposal “would limit the ability of prosecutors to inflate sentences by stacking multiple charges for the same conduct and turning non-felony charges (punishable by imprisonment for a year or less) into felonies.”
At the same time, the proposal’s authors say their offering would get rid of vague language that has up until now given prosecutors a wide berth with regards to charging suspected computer criminals. The reintroduction of the act removes the definition of “exceeds authorized access” that is currently on the books, and in its place outlines new terms for accessing a computer “without authorization.”
“The proposed changes make clear that CFAA does not outlaw mere violations of terms of service, website notices, contracts or employment agreements,” Aaron’s Law’s sponsors said this week.
Violating an app’s terms of service or sharing academic articles should not be punished more harshly than a govt agency hacking Senate files
— Ron Wyden (@RonWyden) April 21, 2015
“Violating a smartphone app’s terms of service or sharing academic articles should not be punished more harshly than a government agency hacking into Senate files,” Wyden said in a not-so-subtle reference to last year’s scandal surrounding the Central Intelligence Agency’s eavesdropping on congressional staffers involved in investigation the CIA. “Aaron’s Law would curb this abuse while still preserving the tools needed to prosecute malicious attacks.”
Thirty-years of cyber prosecutions
The CFAA was signed into law in 1984 by then-President Ronald Reagan, and was reportedly the commander-in-chief’s response, at least in part, to the fictional movie “War Games.” In The film, a computer whiz accidentally breaches the network of the North American Aerospace Defense Command and comes close to starting a new global war.
"I don't understand these computers very well, but this young man obviously did. He had tied into NORAD!" Reagan told a group of Democratic lawmakers after watching the movie, according to an acclaimed account of his time as president, which was published by journalist Lou Cannon in 2000.
Nearly 30 years after the CFAA was signed into law, prosecutors used it to go after suspected computer criminals in excess of 80 times a year, according to remarks made by George Washington University law professor Orin Kerr last December, during a panel hosted by the Cato Institute.
Others to be charged with CFAA violations include WikiLeaks source Chelsea Manning, who was convicted of violating the law’s provisions for unlawfully accessing classified documents from a military computer, and Jeremy Hammond, the hacktivist who breached the network of a private intelligence firm in 2012 and stole a trove of sensitive and revealing emails.
Security researchers have also suffered from CFAA prosecutions. An offering made from the White House earlier this year that the administration said would modernize the computer bill, elevated those concerns among experts despite government assurances.
Kerr, the Georgetown professor, wrote in the Washington Post that the White House’s recent proposal, presented in the wake of last year’s major Sony Picture Entertainment hack, “would seem to allow lots of prosecutions under a ‘you knew the computer owner wouldn’t like that’ theory.’” Mark M. Jaycox, a legislative analyst for the Electronic Frontier Foundation, a digital rights group, said the EFF was “shocked by the proposed changes.”
With respect to the latest proposal regarding CFAA reform, Lofgren and Wyden are already receiving support. The lawmakers introduced Aaron’s Law this week alongside Sen. Rand Paul (R-Kentucky), the 2016 presidential hopeful, and Representatives Jim Sensenbrenner (R-Wisconsin), Mike Doyle (D-Pennsylvania) Dan Lipinski (D-Illinois) and Jared Polis (D-Colorado). They were all listed as co-sponsors in a statement published this week.
"I am proud to join Sen. Wyden and Rep. Lofgren today in offering this bipartisan and bicameral legislation which will amend the Computer Fraud and Abuse Act," Paul said in a statement. "Aaron's Law will reduce overbroad prosecutions and adjust unfair sentencing practices."
Others say that resolving issues with the CFAA might be best settled by eradicating the law completely. "I don't see why we need a CFAA at all,” Andrew Auernheimer, a previously-convicted CFAA violator, told RT on Wednesday. “The cybercrime we all want to stop is already covered by federal wire fraud statutes. If someone steals a million dollars, he should be punished for that, but not extra because he used a computer.”
“This law has been solely used to attack political activists. Editing isn't enough. We need a full repeal,” Auernheimer told RT’s Andrew Blake.
Auernheimer was convicted in 2013 of violating the CFAA after a security team he was involved in, publicized an embarrassing security flaw on the website of telecom giant AT&T that affected owners of the Apple iPad. He was sentenced to 41 months in prison, but a legal team, led by Kerr, successfully had the conviction overturned last year.












