Feds investigating two dozen potential hacks targeting life-saving medical devices
Published 22 Oct, 2014 20:36 | Updated 22 Oct, 2014 20:36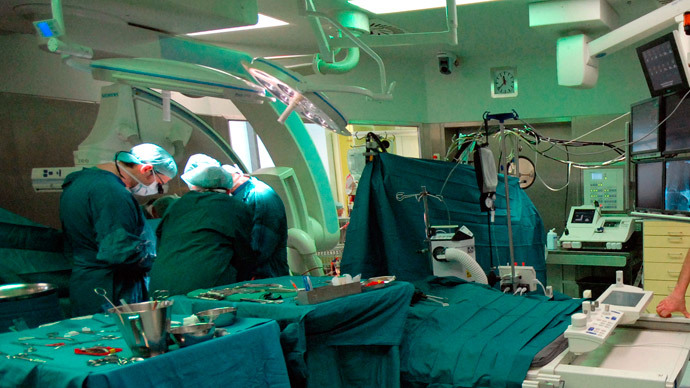
A senior official at the Department of Homeland Security tells Reuters that government experts are now investigating upwards of two dozen instances in which high-tech medical products may be prone to hackers.
"It isn't out of the realm of the possible to cause severe injury or death," the DHS source, who spoke on condition of anonymity, said of the potential consequences that could occur if the devices in question are exploited by malicious actors.
According to the Reuters article published on Wednesday this week by journalist Jim Finkle, the DHS Industrial Control Systems Cyber Emergency Response Team, or ICS-CERT, is reviewing “about two dozen cases of suspected cybersecurity flaws” among products alleged to include an infusion pump from Hospira Inc and implantable heart devices from Medtronic Inc and St Jude Medical Inc.
Multiple sources told Finkle that the DHS team has failed to find any evidence so far that vulnerabilities in these devices have been exploited, but nonetheless are working with the manufacturers of the items to examine and audit any computer bugs that risk being compromised.
S.Y. Lee, a spokesperson for DHS, told SCMagazine on Wednesday that the agency “actively collaborates with public and private sector partners every day to identify and reduce adverse impacts on the nation's critical cyber systems,” but declined to answer specifics; Medtronic and St. Jude Medical did not immediately return the magazine’s requests for comment, but a rep for Hospira told Reuters that the company “has implemented software adjustments, distributed customer communications and made a commitment to evaluate other changes going forward, while ensuring we are not adversely impacting the ability of our devices to meet hospital and patient needs, and maintain compliance with FDA product requirements.”
The Reuters report this week was published in the midst of a two-day conference held in conjunction by the United States Food and Drug Administration, the Department of Health and Human Services and the DHS. According to the event’s itinerary, two topics in particular that were slated to be explored this week include “Gaining situational awareness of the current cyber threats to the HPH Sector including those that impact medical devices” and “Identifying cybersecurity gaps and challenges, especially end-of-life support for legacy devices and interconnectivity of medical devices.”
Although Reuters has not identified any instances in which hackers have exploited such vulnerabilities, Finkle wrote that sources suggested DHS “is concerned that malicious actors may try to gain control of the devices remotely and create problems, such as instructing an infusion pump to overdose a patient with drugs, or forcing a heart implant to deliver a deadly jolt of electricity.”
ICS-CERT first warned in 2013 that security researchers had discovered a vulnerability affecting around 300 medical devices sold through about 40 vendors, the likes of which “could be exploited to potentially change critical settings and/or modify device firmware.” That summer, acclaimed security researcher Barnaby Jack was scheduled to show at a Las Vegas hacker convention how pacemakers are prone to hackers, but passed away days before the event; his death was later ruled an overdose.
“I was intrigued by the fact that these critical life devices communicate wirelessly. I decided to look at pacemakers and ICDs (implantable cardioverter defibrillators) to see if they communicated securely and if it would be possible for an attacker to remotely control these devices,” Jack, who previously demonstrated a hack affecting insulin pumps, told Vice last year. “If the devices can be accessed remotely, there's always a potential for abuse.”
Only weeks ago, the FDA said it was finalizing recommendations intended to advise medical product manufacturers of potential cybersecurity risks.
“There is no such thing as a threat-proof medical device,” Suzanne Schwartz, M.D., MBA, the director of emergency preparedness/operations and medical countermeasures at the FDA’s Center for Devices and Radiological Health, said earlier this month. “It is important for medical device manufacturers to remain vigilant about cybersecurity and to appropriately protect patients from those risks.”
"The conventional wisdom in the past was that products only had to be protected from unintentional threats,” William Maisel, a chief scientist at the same FDA office, told Reuters this week. “Now they also have to be protected from intentional threats too.”