US blames Moscow for NotPetya malware, which hit Russia too
Published 16 Feb, 2018 02:22 | Updated 20 Feb, 2018 13:02
The White House has blamed the Russian military for the NotPetya malware attack, which hit major companies and government systems across the globe in June 2017, including in the US, UK, Ukraine and Russia.
In a statement on Thursday, the White House publicly condemned the Russian military for launching "the most destructive and costly cyber-attack in history," which they estimated caused "billions of dollars in damage across Europe, Asia, and the Americas."
Washington alleged that the attack “was part of the Kremlin’s ongoing effort to destabilize Ukraine," adding that it "demonstrates ever more clearly Russia’s involvement in the ongoing conflict." The White House threatened that the attackers "will be met with international consequences."
The US is now “reviewing a range of options” in response to the attack, a White House official told Reuters.
The Ukrainian government, airports, banks and other financial institutions were reportedly the first to be hit by the cyber-attack, which quickly spread to other parts of the world. The attack also crippled West Virginia Health System and hospitals in the US, Danish international shipping company and energy conglomerate Moller-Maersk, FedEx subsidiary TNT, as well as the Russian state oil giant Rosneft and many others businesses in 64 countries.
It was estimated that the losses inflicted by the malware could run as high as $53 billion. Maersk reported losses of $200-300 million as result of the attack and FedEx estimated its damages at $300 million.
Several Russian companies were also hit, including metal maker Evraz, and oil giant Rosneft. Despite the malware’s global outreach, Kiev immediately pointed a finger at Moscow.
The White House’s statement implicating Russia in the attack came hours after the UK Foreign and Defense ministries initially accused the Russian government.
“The attack showed a continued disregard for Ukrainian sovereignty. Its reckless release disrupted organizations across Europe costing hundreds of millions of pounds,” UK Foreign Foreign Office Minister for Cyber Security Lord Tariq Ahmad said, adding that “the UK and its allies will not tolerate malicious cyber activity.”
Neither the UK nor the US provided any explanation as to why they pinned the blame on Russia.
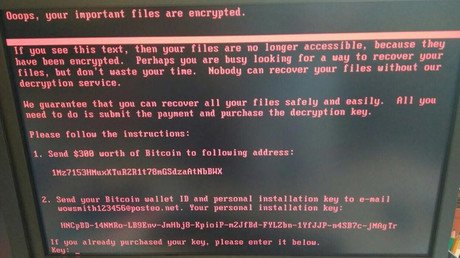
The malware earned the name “NotPetya” because of its code, which resembled an earlier ransomware called Petya. However, researchers from Kaspersky Labs argued it that it was a wiper disguised as ransomware, and it was aimed at destroying data rather than extortion.
The Kremlin has denounced the latest spin as a new manifestation of the Russophobia that has been rife in the West, calling the accusations “unsubstantiated and groundless.”
Danish Defense Minister Claus Hjort Frederiksen has joined the chorus of accusations against Russia, saying that it could be “compared with a military attack,” while addressing a NATO defense ministry meeting in Brussels.
Upon consulting with the US and the UK, Austrailia has joined in on blaming Russia for NotPetya. Australia’s Minister for Law Enforcement and Cyber Security Angus Taylor said that the government “judged that Russian state sponsored actors were responsible for the incident.”
Less than a month after the attack, NATO claimed that it could “most likely be attributed to a state actor” and warned of international retaliation. At the time, NATO Secretary General Jens Stoltenberg said that a cyber-attack against a NATO member could be enough to invoke Article 5 of the NATO treaty, hinting at a potential military response. Ukraine, which is seeking to become a NATO member under the current pro-Western government, is currently not a member of the block.