Who's watching you? Surveillance cameras are easy targets for hackers
Published 15 May, 2012 22:46 | Updated 16 May, 2012 18:05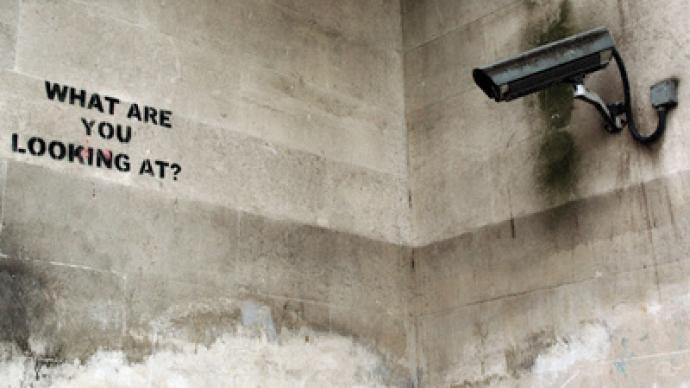
It’s not news that surveillance cameras are practically everywhere in America, but do you know who exactly is monitoring your every move? One security expert has the answer, and it isn’t pretty.
Researcher Justin Cacak of Gotham Digital Science has been investigating some of the country’s most popular closed-circuit surveillance camera systems and has come to a startling discovery: hacking into the feed of hidden cam is often feat even a novice computer nerd can manage.Speaking to Wired this week, Cacak reveals that much of the US relies on CCTV systems from only a few big name companies. Of those, he says, MicroDigital, HIVISION and CTRing are the most popular. So popular, in fact, that many of their customers simply purchase their products, install them with ease and assume they are good to go. Rarely, he says, does it seem that administrators bother to change the default passwords of these out-of-the-box systems.And since many CCTV systems come ready to broadcast to the Web, hackers can access them from around the globe.“You can essentially view these devices from anywhere in the world,” Cacak tells Wired.The researcher adds that his team examined more than 1,000 closed-circuit TV cameras that had Internet capabilities and could also be hacked with just a little bit of the right know-how. Most of the major brands come with remote Internet access enabled by default, reports the website, and unless an administrator takes it upon his or herself to disable this service or make a different password, cracking into the system is as easy as making a few educated guesses.“We find about 70 percent of the systems have not had the default passwords changed,” he says.Often those default passwords aren’t very hard to crack either. He says that usually the administrator’s log-in is, predictably, “admin,” or, in some cases, “user.” Passwords are often easy-to-guess numerical codes, such as “1234” or “1111.”“All the ones we found have remote access enabled by default,” Cacak says. “Not all the customers may be aware [of this]…. Because most people view these [video feeds] via console screens, they may not be aware that they can be remotely accessed.”In all of these instances, Cacak says his fellow researchers were hired to audit surveillance systems to search for security vulnerabilities. He might have a big client on his hands if he decides to undertake any work for Illuminating Concepts, though — that’s the company RT reported on last year by revealing that their patented streetlights that double as surveillance hubs had been installed in the city of Farmington Hills, Michigan. Only this week, however, has it been confirmed that the lampposts — which also have the capabilities to broadcast WiFi signals and spy on passersby with cameras — will be coming across the country. Illuminating Concepts say that they have plans to implement their Intellistreets system from coast to coast soon.