Bush cyberczar: NSA created ‘the potential for a police state’
Published 25 Feb, 2014 19:02 | Updated 25 Feb, 2014 19:02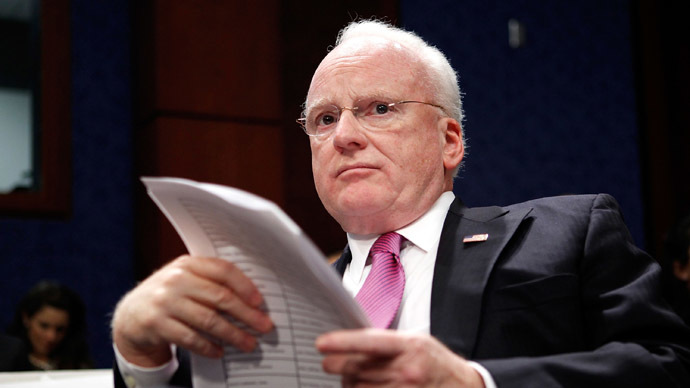
The former cyber advisor under President George W. Bush had some harsh words for the United States National Security Agency during an address in California on Monday: "get out of the business of fucking with encryption standards.”
That was the recommendation that famed cyberczar Richard Clarke made while speaking earlier this week at the at the Cloud Security Alliance summit in San Francisco.
Clarke, 63, served as a counterterrorism advisor for President Bill Clinton in the 1990s and later assisted his successor, Mr. Bush, as the special advisor on cybersecurity for that administration through 2003. Most recently, though, Clarke was assigned to a five-person panel assembled by Pres. Obama late last year that was tasked with assessing the NSA’s operations in the midst of ongoing and ever-damaging leaks disclosed by former intelligence contractor Edward Snowden. In December, that group suggested 46 changes for the Obama administration to consider in order rein in the secretive spy agency.
Speaking during Monday’s conference, however, Clarke opened up about some of the more personal suggestions he has for the NSA, and even some insight about what the future may have in store for the agency if they continue to collect intelligence from seemingly all corners of the Earth.
"In terms of collecting intelligence, they are very good. Far better than you could imagine," Clarke said. "But they have created, with the growth of technologies, the potential for a police state."
"If you're not specific, an agency that bugs phones is going to bug phones," he added, according to the Tech Target blog, Search Security. "The NSA is an organization that's like a hammer, and everything looks like a nail."
Even if the NSA scales back such hacking operations in the future as Pres. Obama suggested and limits who the US targets and how, Clarke said during Monday’s address that another type of interference favored by the agency — influencing and intentionally degrading encryption standards — need to be scraped.
Since June, those Snowden leaks have exposed an array of previously covert NSA operations, including programs that put the emails of foreign leaders and phone data pertaining to millions of Americans into the hands of the US government. According to Clarke, though, the NSA’s handling of encryption standards — as exposed by Snowden — has serious repercussions.
In September, leaked documents courtesy of Mr. Snowden showed the NSA has invested millions of dollars to be able to decrypt “large amounts” of supposedly secure data, an operation that spies at Britain’s GCHQ called “an aggressive, multipronged effort to break widely used Internet encryption technologies.” Then in December, further Snowden documents showed that RSA, a private company considered a staple of the computer security industry, had secretly entered into a $10 million contract with the NSA to create a government-friendly “backdoor” in its products.
Because of the NSA’s efforts, Clarke said during Monday’s event, “the trust in encryption has been greatly eroded.”
“The encryption standards need to be trusted,” he said, according to Infosecurity Magazine. “The US government has to get out of the business of fucking around with encryption standards.”
“We need to rebuild the trust in encryption; we need to have the US government forced some way into ensuring this happens,” he said.
When Clarke and four other Obama-appointed experts weighed in on the NSA’s programs for the report released in December, the group said they were “unaware of any vulnerability created by the US government in generally available commercial software that puts users at risk of criminal hackers or foreign governments decrypting their data. Moreover, it appears that in the vast majority of generally used, commercially available encryption software, there is no vulnerability, or ‘backdoor,’ that makes it possible for the US government or anyone else to achieve unauthorized access.”
As part of the group’s recommendations, they advised that the NSA “not engineer vulnerabilities into the encryption algorithms that guard global commerce” and “not demand changes in any product by any vendor for the purpose of undermining the security or integrity of the product, or to ease NSA’s clandestine collection of information by users of the product.”














