Hackers retrieve $140K+ in WannaCry ransom
Published 3 Aug, 2017 21:35 | Updated 4 Aug, 2017 07:23
An unidentified person has cashed out more than $140,000 worth of bitcoins in ransom collected from victims of the WannaCry’s global computer hack. WannaCry encrypted users’ files, and hackers charged $300 to $600 for keys to get the files back.
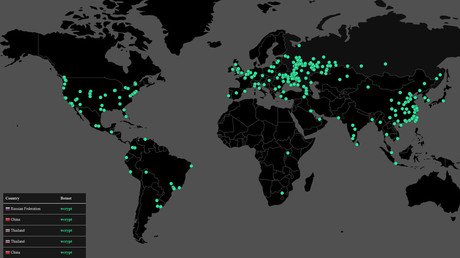
The ransomware virus hit hundreds of thousands of computers around the world in May, targeting hospitals, business and government systems. For three months the ransom money sat untouched in three bitcoin wallets.
A Twitter bot called @actual_ransom, set up by the media outlet Quartz to watch the bitcoin accounts, picked up the first withdrawal at 11:10 pm on August 2.
Status of WannaCry wallets:
— actual ransom (@actual_ransom) July 31, 2017
52.19666422 BTC ($141,703.77)
338 payments, 0 withdraws
Last payment:
2017-07-24 at 10:07 AM ET
🚨 7.34128314 BTC ($20,055.52 USD) has just been withdrawn from a bitcoin wallet tied to #wcry ransomware. https://t.co/wX2k9pJLNQ
— actual ransom (@actual_ransom) August 3, 2017
Within ten minutes, the full amount was withdrawn in increments of around $20,000 from the three bitcoin accounts and sent to nine other accounts.
🚨 9.67641378 BTC ($26,508.37 USD) has just been withdrawn from a bitcoin wallet tied to #wcry ransomware. https://t.co/CJLiu6cyvr
— actual ransom (@actual_ransom) August 3, 2017
Europol, the European Union’s law enforcement agency, said the investigation into WannaCry is ongoing and declined to comment on the latest developments.
It's Happening ... Finally! Hackers Behind #WannaCry Ransomware Withdraw $143,000 From #Bitcoin Wallets https://t.co/NtkRiYlADlpic.twitter.com/1Xfc6cibWz
— The Hacker News (@TheHackersNews) August 3, 2017
The WannaCry ransomware attack targeted computer running the Microsoft Windows operating system and within a day infected more than 230,000 computers in over 150 countries. The four countries most affected were Russia, Ukraine, India and Taiwan.
The attack could have been much worse if not for the UK researcher Marcus Hutchins discovering a “kill switch,” using a call-and-response with a hardcoded URL. Hutchins, 22, runs a blog called Malware Tech.
Melanie Shapiro, CEO of identity security firm Token, told CNN the funds in the bitcoin accounts are probably being moved to make them less traceable. The process is called “tumblers,” and the smaller amounts make the transactions harder to track.
"We can watch all of this bitcoin be moved around, but inevitably every move makes it harder to trace back to an individual," she said.
Bitcoin transactions and accounts are public, but they are also anonymous.
However, investigators told CNN Money that even with the dispersal to nine other accounts, they will be able to see a trail of digital breadcrumbs leading from account to account.
A number of security experts, including those at Kaspersky Lab, have linked the WannaCry attacks to North Korea’s Lazarus Group, an outfit either within that country’s government or acting on its behalf.
In an interesting twist, WannaCry hero Hutchins was arrested by the FBI on Wednesday in Nevada for his role in creating and distributing the Kronos banking Trojan, Motherboard reported citing a Justice Department spokesperson.
The charges against him relate to alleged conduct occurring between July 2014 and July 2015. The trojan stole credentials and personal information and put malicious code on victims’ computers.
The Eastern District of Wisconsin returned a six-count indictment against Hutchins on July 12, 2017. It was unsealed at the time of his arrest.