Police can use Stingray surveillance devices to listen to calls – documents
Published 29 Oct, 2015 17:16
It’s long been known that authorities can use the secretive Stingray tools to track people by their cell phones. Now it’s been revealed that police are actually able to listen in on calls using the device.
Stingrays, cell-site simulators, are suitcase-sized devices that work by mimicking cell towers and intercepting the signals of mobile phones. This can be used to get information on the contacts, messages and even location of the owner of a phone, making its use by police and federal agencies controversial.
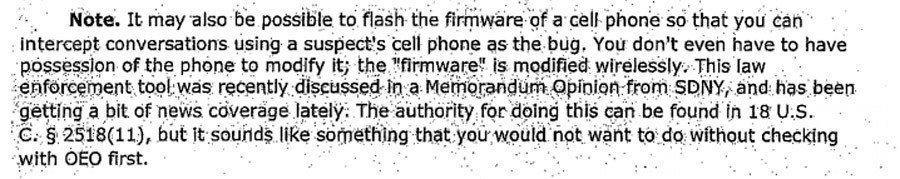
Now, new Department of Justice documents have revealed that Stingrays also allow the users of the device to snoop on phone calls and record the numbers of outgoing calls. The documents, which function as guidelines for the use of Stingrays by law enforcement, also discussed the possibility of replacing a phone’s firmware so that users “can intercept conversations using a suspect’s cell phone as a bug. You don't even have to have possession of the phone to modify it; the 'firmware' is modified wirelessly.”
Only after a protracted legal battle was the American Civil Liberties Union of Northern California able to get the documents from the Justice Department, in which they acknowledge the controversy surrounding Stingrays.
The documents say that when using a Stingray to identify a phone a suspect is using, agents should limit their snooping to gathering device-identifying information. “It should not encompass dialed digits, as that would entail surveillance on the calling activity of all persons in the vicinity of the subject,” the guidelines read.
Need stingray surveillance? Get a warrant! California gov signs landmark privacy law http://t.co/eV1F9MTyEdpic.twitter.com/thwg1Kgeoh
— RT America (@RT_America) October 9, 2015However, this type of restraint is only spelled out because the devices have such far-reaching functionality, including the ability to actually hear the contents of intercepted calls. The DoJ goes on to note that the devices “may be capable of intercepting the contents of communications and, therefore, such devices must be configured to disable the interception function, unless interceptions have been authorized by a Title III order.”
Title III is the part of the law that gives the authorities the power to perform a wiretap – that is, listen to calls in real-time – and authorities who wish to perform a wiretap need to get a warrant.
The newly-revealed documents only confirm the suspicion of privacy advocates, who have long suspected that Stingrays have the capability to gather the contents of communications, not just the metadata.
This revelation comes less than a week after the Guardian obtained another set of documents showing that the IRS bought the cell-site simulators from Harris Corporation in 2009 and 2012. This makes the IRS the 13th.
Revealed: IRS owned Stingray cellphone surveillance equipment https://t.co/wwPl59JlLFpic.twitter.com/9oGc6t6tgK
— RT America (@RT_America) October 26, 2015In addition to federal agencies, 56 state or local police departments in 22 states and the District of Columbia own Stingrays, the American Civil Liberties Union says, but a lack of transparency in the use and ownership makes it impossible to know the scale of the surveillance that the devices facilitate.














