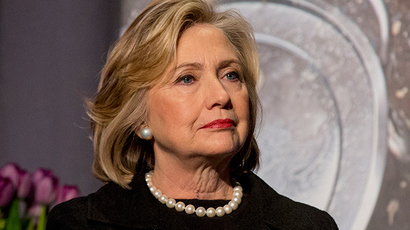
Hillary’s private email server was insecure during first 3 mths as secretary of state
Published 12 Mar, 2015 21:08 | Updated 12 Mar, 2015 20:53
For the first three months Hillary Clinton was secretary of state, her private email server was not encrypted, according to a new report. That left her communications vulnerable while she conducted government business, including international travel.
During her four years in office, Clinton conducted all of her state business using a private email account administered from her family home, instead of an official State Department domain. That revelation has raised questions about the security of her communications.
Kevin Bocek, vice president of security strategy and threat intelligence at Venafi security company, wrote in a blog post that encryption was enabled on Clinton’s server in 2009, and will be enabled through at least 2018. However, for the first three months Clinton was at the State Department ‒ January through March 2009 ‒ such encryption did not exist.
READ MORE: Colin Powell also used personal email at State Dept., but was it illegal?
The company used “non-intrusive Internet scanning routinely performed throughout the IT security community to protect the safety and health of the Internet” to analyze the security on Clinton’s email server during her time as the country’s top diplomat. Specifically, Venafi looked at the digital certificates used with clintonemail.com since January 2009.
“A digital certificate is an electronic ‘passport’ that allows a person, computer or organization to exchange information securely over the Internet,” TechTarget Network explained. “Just like a passport, a digital certificate provides identifying information, is forgery resistant and can be verified because it was issued by an official, trusted agency.”
“This means that during the first 3 months of Secretary Clinton’s term in office, web browser, smartphone, and tablet communications would not have been encrypted. Attackers could have eavesdropped on communications,” Bocek wrote. “As well, the server would not have been uniquely identified as being clintonemail.com and therefore could have been spoofed – allowing attackers to more easily trick an unsuspecting user of the site to hand over their username and password or other sensitive information.”
The former secretary of state has promised critics that her email was secure.
“The system we used was set up for Pres. Clinton’s office and it had numerous safeguards,” Clinton said on Tuesday. “It was on property, guarded by the Secret Service and there were no security breaches. So I think that the use of that server which started with my husband certainly proved to be effective and secure.”
READ MORE: Hillary Clinton claims e-mail system installed for Bill was 'effective & secure'
During the time the system wasn’t encrypted, Clinton traveled to China, Egypt, Israel, South Korea and other international locations.
"It is almost certain that at least some of the emails hosted at clintonemails.com were intercepted," independent security expert and developer Nic Cubrilovic told Gawker.
Clinton’s encryption used a commercial product from Fortinet, security experts who examined the system told Bloomberg. Alex McGeorge, head of threat intelligence at Immunity Inc., a digital security firm, was one of them. He found that the setup used a default encryption certificate ‒ not one purchased specifically for Clinton’s server.
“It’s bewildering to me,” McGeorge said. “We should have a much better standard of security for the secretary of state.”
Fortinet issued a statement saying it wasn’t aware the company’s technologies were used by Clinton.
“If they were, our recommendation is to replace provided self-signed certificates with valid digital certificates for the protected domains,” said Andrea Cousens, a Fortinet spokeswoman.
Clinton email server not encrypted or authenticated by a digital certificate for first three… http://t.co/KH0Nsfwlrrpic.twitter.com/0UzZ8Olhig
— Tony Manning (@ManningT) March 12, 2015
Clinton likely hired an expert to configure the communication channel for her, Tim ‘T.K.’ Keanini, chief technology officer for network security company Lancope Inc., told Bloomberg.
But one expert ‒ or even a small team of them ‒ doesn’t compare to an entire IT department when it comes to monitoring and security.
“There are tons of disadvantages of not having teams of government people to make sure that mail server isn’t compromised,” McGeorge said. “It’s just inherently less secure.”
“Unless she was employing 24-by-7 advanced monitoring, protection and incident response, I just don’t see how she could have as secure a system,” Jason Straight, chief privacy officer for UnitedLex, which advises corporations on cybersecurity practices, told the Hill. “I just don’t see how on a day-to-day basis with all of the maintenance, monitoring and detection that had to happen that she could have reasonably paid to have the level needed.”
READ MORE: State Dept criticized, sued over handling of Clinton-era emails
The Department of State has “no indication that Secretary Clinton used her personal email account for anything but unclassified purposes,” Deputy Press Secretary Marie Harf said.
But that would have made little different to foreign intelligence agencies, security experts told the Hill, noting that the National Security Agency targeted German Chancellor Angela Merkel’s personal, unclassified cell phone.
“It’s likely been something that foreign intelligence agencies have had their eyes on for many years,” Christopher Soghoian, principal technologist for the American Civil Liberties Union (ACLU). said. “It’s irresponsible for the top U.S. diplomat to be putting communications at risk in that way. After the president, Secretary Clinton was probably the highest value target for foreign intelligence agencies.”
In fact, Germany's foreign intelligence agency intercepted at least one phone call made by Clinton, when her phone was tapped “accidentally” while she was on a US government plane.