FBI pretended to be Seattle newspaper in order to hack suspect’s computer
Published 28 Oct, 2014 18:03 | Updated 28 Oct, 2014 21:06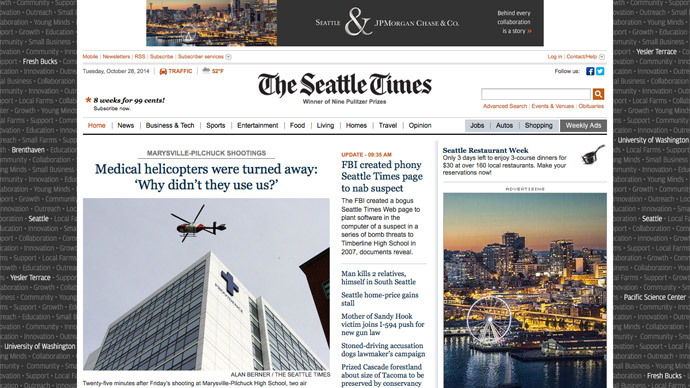
The editor of the Pulitzer Prize-winning Seattle Times newspaper says she’s “outraged” to learn only this week that the FBI made a mock-up of the publication’s website in 2007 in order to spread spyware onto the computer of a suspect.
When agents with the Seattle division of the FBI swarmed the home of a 15-year-old high school student that year and charged him with making bomb threats, media reports noted that the arrest was made possible with the use of a so-called “Computer & Internet Protocol Address Verifier” program, or CIPAV, that had been remotely installed on the individual’s machine to collect and then communicate to the authorities the user-specific information that eventually identified the suspect. The student later pleaded guilty to emailing repeated bomb threats to Timberline High School and was sentenced to 90 days in juvenile detention.
Until this week, how the FBI actually went about sneaking the CIPAV program onto the student’s computer was a matter that went unreported. After digging through a trove of emails previously obtained through a Freedom of Information Act request, however, American Civil Liberties Union technologist Chris Soghoian stumbled upon details this week showing that authorities accomplished the installation by sending a malicious link disguised as a Seattle Times news article to a social media account used by their suspect.
The FBI impersonates AP/Seattle Times articles to deliver malware to suspects. Pretty despicable. via @csoghoianpic.twitter.com/DVnslq8Pcn
— Trevor Timm (@trevortimm) October 27, 2014
"Here is the email link in the style of the Seattle Times," reads one of dozens of internal FBI emails spotted by Soghoian on Monday as he combed through details concerning the bureau’s use of the spyware.
“[B]elow is the news article we would like to send containing the CIPAV. I am meeting with the judge at 1:30 PST and hope to deploy afterwards,” reads another.
According to the correspondence, the FBI’s plan involved sending a fake Seattle Times article to a MySpace account that was purported to be created by the person responsible for repeatedly making phony bomb threats. The link, which was supposed to direct the visitor to an Associated Press article called “Bomb threat at high school downplayed by local police department,” was hosted on a FBI computer, however, and, when clicked, covertly infected the target’s machine.
Once the MySpace user navigated to the phony Times article, the CIPAV was silently installed and soon began sending investigators information about the IP address associated with the computer’s browsing history, as well as details about other sites that were being visited and machine-specific specs that made it possible for investigators to draft charges and issue an arrest for the minor.
Although the seven-year-old operation hasn’t made headlines since the student was sentenced in July 2007, the investigation is now making waves after it was revealed through Soghoian’s discovery that not only did the FBI pose as the press to infect a suspect’s computer, but that The Seattle Times were never told by the feds that their name was used to hack a high school student.
After Soghoian fired out a barrage of tweets concerning his discovery on Monday, the Times published an article of their own — one presumably free of malware — denouncing what the paper considers to be an act of “deception” carried out by federal authorities.
“We are outraged that the FBI, with the apparent assistance of the US Attorney’s Office, misappropriated the name of The Seattle Times to secretly install spyware on the computer of a crime suspect,” Seattle Times Editor Kathy Best said late Monday. “Not only does that cross a line, it erases it.”
“Our reputation and our ability to do our job as a government watchdog are based on trust. Nothing is more fundamental to that trust than our independence — from law enforcement, from government, from corporations and from all other special interests,” Best added. “The FBI’s actions, taken without our knowledge, traded on our reputation and put it at peril.”
The FBI is standing by its behavior, however, saying in response that investigators were in the right to rely on the previously undisclosed tactic to prevent a "possible act of violence in a school setting,” even evoking a Washington state school shooting from earlier this week to defend the bureau’s actions.
“Every effort we made in this investigation had the goal of preventing a tragic event like what happened at Marysville and Seattle Pacific University,” FBI Agent Frank Montoya Jr. told Seattle’s The Stranger magazine. “We identified a specific subject of an investigation and used a technique that we deemed would be effective in preventing a possible act of violence in a school setting. Use of that type of technique happens in very rare circumstances and only when there is sufficient reason to believe it could be successful in resolving a threat. We were fortunate that information provided by the public gave us the opportunity to step in to a potentially dangerous situation before it was too late.”
That the FBI impersonated a newspaper's website to deliver malware to a target is outrageous. Over the top crazy.
— Christopher Soghoian (@csoghoian) October 27, 2014
Others, including Soghoian, say the FBI’s action demonstrate an instance in which the bureau has gone well beyond its restraints.
“That the FBI impersonated a newspaper's website to deliver malware to a target is outrageous. Over the top crazy,” Soghoian said on Twitter.
“As outrageous as it is, secretly impersonating newspapers to send malware probably works,” Trevor Timm, the executive director of the Freedom of the Press Foundation, said on Twitter. “You can bet the FBI has done this more than once.”
As outrageous as it is, secretly impersonating newspapers to send malware probably works. You can bet the FBI has done this more than once.
— Trevor Timm (@trevortimm) October 28, 2014
Best, the editor of the Times, told The Stranger on Monday that she can only hope Timm’s tweet doesn't ring true.
“We hope that this mistake in judgment by the FBI was a one-time aberration and not a symptom of a deeper lack of respect for the role of a free press in society,” Best said.
Later, Associated Press spokesperson Paul Colford expressed his disappointed in the FBI with Politico's Hadas Gold.
"We are extremely concerned and find it unacceptable that the FBI misappropriated the name of The Associated Press and published a false story attributed to AP. This ploy violated AP’s name and undermined AP’s credibility," Colford said.













