‘ChewBacca’ Trojan steals thousands of credit card details across the globe
Published 1 Feb, 2014 17:26 | Updated 3 Feb, 2014 08:10
Star Wars’ most loyal copilot has gone to the dark side on our side of the galaxy, as Malware operating under the name ‘ChewBacca’ has stolen data on 49,000 payment cards from 45 retailers in 11 countries over a two month span.
According to RSA FirstWatch, the Security Division of EMC which exposed the malignant software, the virus started running in October and has so far gathered 24 million transaction details, mostly in the US, but also in Canada, Australia and Russia.
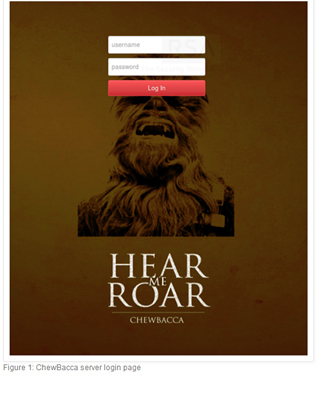
This relatively new Trojan was dubbed ‘ChewBacca’ because an image of the iconoclastic Wookiie was featured on the login page of the server, which the hacking ring used to collect data from infected computers.
Although the Trojan creators had routed stolen data through the Tor network that enables online anonymity, Massachusetts-based RSA managed to locate them and passed the information on its location to the FBI.
RSA researchers have also communicated with the companies victimized by the malware during the shutdown operation, which has yet to end, to share the gathered information.
‘ChewBacca’ features “simple keylogging and memory-scraping functionality”, the RSA said in its blog. Its target is mainly systems that process credit cards, such as Point-of-Sale (POS) systems.
The Trojan “is self-contained and runs as-is”. It installs a copy of itself in the Windows Startup folder and its memory scanner searches for credit card information in a copy of a process’s memory, targeting at simple regular expressions for card magnetic stripe data, the RSA said. Once extracted, it is sent to the server via Tor.
In fact, ‘ChewBacca’ was first revealed in December by Kaspersky Lab. At that time the Lab pointed out that the Trojan was not for sale on underground forums and seemed to be for private use or in development.
‘ChewBacca’ comes in a wave of malware attacks, aimed at making computers vulnerable in order to steal data from them. Another notorious 2013 example, ‘Dexter’, named after a serial killer from the popular television series, caused huge losses in the restaurant and hotel industry worldwide.
Among the shops that suffered from such attacks was Target Corp., where hackers stole some 40 million payment card numbers and other data from around 70 million customers, Reuters reports. Another victim of infectious malware was the luxury department store Neiman Marcus.
The FBI has issued a warning to on-line retailers, urging them to strengthen security and alerting them of possible attacks.












