Keyboard app security gaffe exposes 31mn users’ data including passwords, web searches
Published 6 Dec, 2017 04:38 | Updated 6 Dec, 2017 05:05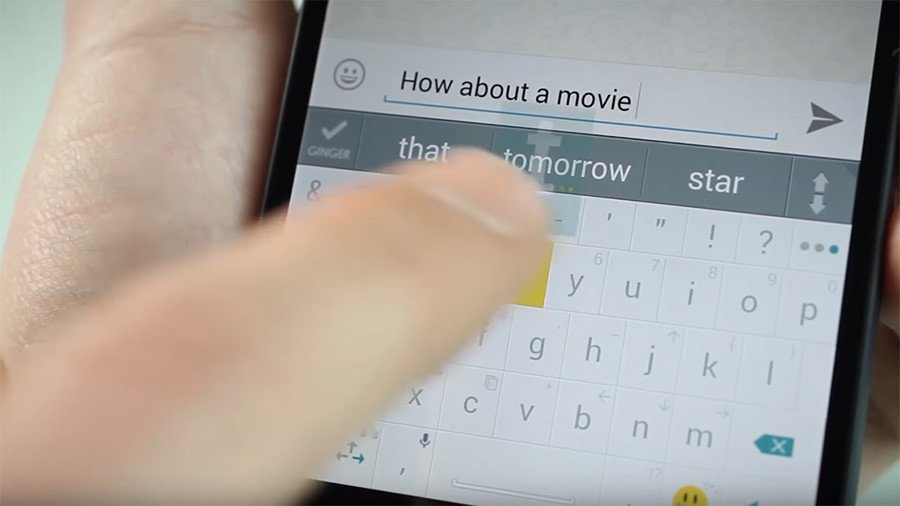
More than 31 million users of a popular virtual keyboard app AI.type, have had their private data exposed online, including email addresses, passwords, dates of birth and details from Google accounts, as well as actual text entered using the keyboard.
AI.type is an onscreen keyboard with 40 million users. It has a free and paid version, and, according to its privacy policy, users who have the free version have more of their data collected. The company uses this to sell advertising, ZDnet reports.
The breach occurred when the company failed to secure the server with a password, leaving it exposed to hackers. It was uncovered by Kromtech Security Center researchers. AI.type is owned by Eitan Fitsui, who acknowledged the breach but didn’t comment further.
“Theoretically, it is logical that anyone who has downloaded and installed the Ai.Type virtual keyboard on their phone has had all of their phone data exposed publicly online,” Bob Diachenko of Kromtech told ZDNet. “This presents a real danger for cyber criminals who could commit fraud or scams using such detailed information about the user.”
Some 577 gigabytes of data only appears to include Android users’ details. It includes email addresses, exact locations and full names. Data collected from free users includes their phone’s unique IMSI and IMEI numbers, SIM cards and mobile networks, and what version of Android the phone has.
In some cases, phone numbers, IP addresses, internet provider and even Google profiles were captured. Information included in the Google profiles entails email addresses, profile photos and dates of birth, some of which lists of every app installed on a person’s phone.
The compromised data also includes a collection of over 8.6 million text entries captured from the keyboard, which included web search terms and passwords. ZDnet also uncovered users’ address book contact details, with one collection containing 10.7 million email addresses.














