Not just listening: Samsung TVs send out unsafe ‘unencrypted’ data
Published 19 Feb, 2015 20:02 | Updated 19 Feb, 2015 20:02
Not only do Samsung TVs “listen in” on their owners, but when they do, they send data to third parties without any encryption – making it easier to intercept and decode.
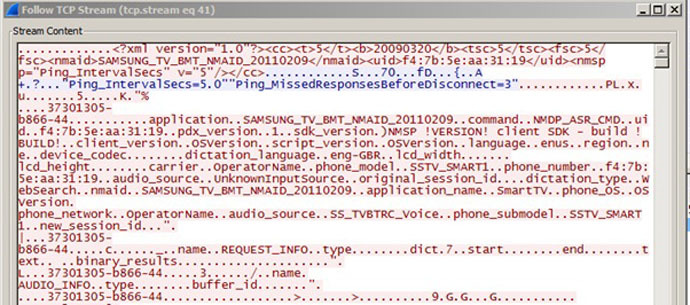
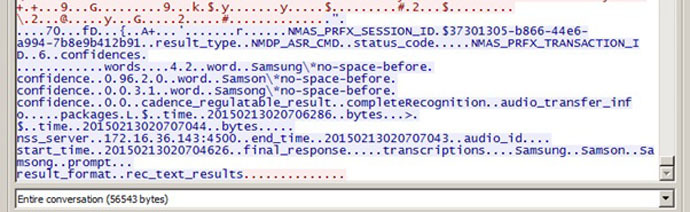
Well-known security researcher David Lodge from Pen Test Partners conducted an attempted interception of a data packet sent from a Samsung Smart TV, which receives data spoken into a microphone attached to a remote, and sends it to the internet for interpretation.
Lodge was surprised to discover that the data packets lacked encryption – commonly used when sensitive data is being transferred - so the words he spoke to the set could be discerned as such in the data file.
READ MORE: Careful what you say: Your Samsung TV might be listening
“What we can see is it sending a load of information over the wire about the TV, I can see its MAC address and the version of the OS in use. After the word buffer_id is a load of binary data, which looks audio-ish,”explained Lodge. “Based on the limited information leaked above in plaintext, there’s plenty to suggest that interesting data is making its way on to the interwebs from your TV. Come on Samsung, how about at least protecting it with SSL?”
Accusations of failure to sufficiently encrypt data, and store it only in safe locations, have plagued other online products in recent years, including Skype and chat program Viber.
Samsung said it was working to resolve the issue.
“Samsung takes consumer privacy very seriously and our products are designed with privacy in mind. Our latest Smart TV models are equipped with data encryption and a software update will soon be available for download on other models,” said a statement emailed to the Guardian newspaper.
Last week, there was considerable outcry when Samsung owners discovered that under their terms for using a Smart TV remote, they were warned that “if your spoken words include personal or other sensitive information, that information will be among the data captured and transmitted to a third party through your use of voice recognition.”
It is impossible to access the data packets without hacking into the internet pathway between the TV and the servers to which it sends its data – a task that requires significant expertise, though easily within the scope of the NSA, GCHQ or any other intelligence agency.
Lodge reassures that by design the remote listening function does not record and process data, unless it is switched on by the user, but said that dangers remained.
“The potential for a rogue firmware update enabling ‘snooping’ is significant,” wrote Lodge.










