‘You cannot find us’: Sony hackers leak new data as FBI says no N. Korea trace
Published 9 Dec, 2014 23:06 | Updated 10 Dec, 2014 01:06
The FBI says it cannot confirm whether the computer leak that has devastated Sony Pictures Entertainment was orchestrated by North Korea, or any other entity. Meanwhile, the hackers themselves have posted more threats and confidential data.
“We are the GOP working all over the world,” began the message purportedly from Guardians of Peace, the group that has taken responsibility for the hacks, unveiled on the Github coding website.
“We have already given our clear demand to the management team of SONY, however, they have refused to accept…We are sending you our warning again. Do carry out our demand if you want to escape us,” continues the message, in what appears to be a reference to the extortion demands made by the group in a letter to its top executives, just days before the first breaches became public a fortnight ago via Mashable.
“And, Stop immediately showing the movie of terrorism which can break the regional peace and cause the War!”
The movie in question is 'The Interview,' a Seth Rogen comedy about two news anchors being recruited by the CIA to kill North Korean leader Kim Jong-un, which is scheduled for a Christmas release in the US.
“You, SONY & FBI, cannot find us. We are perfect as much. The destiny of SONY is totally up to the wise reaction & measure of SONY,” ends the message.
The latest leaks, which have been combed by internet security firms, notably include the personal phone numbers and other data belonging to celebrities including as Brad Pitt, Julia Roberts, and Tom Hanks.
For the beleaguered Sony Pictures, this is unlikely to be the most damaging aspect of the disclosure.
The documents reveal thousands of confidential vendor contracts which the studio has signed with all of its partners, from filming equipment providers to the ancillary producers of merchandise that accompanies its latest releases. The trove also contains unreleased scripts and documents pertaining to court cases in which the studio is embroiled – including lawsuits by the Screen Actors Guild.
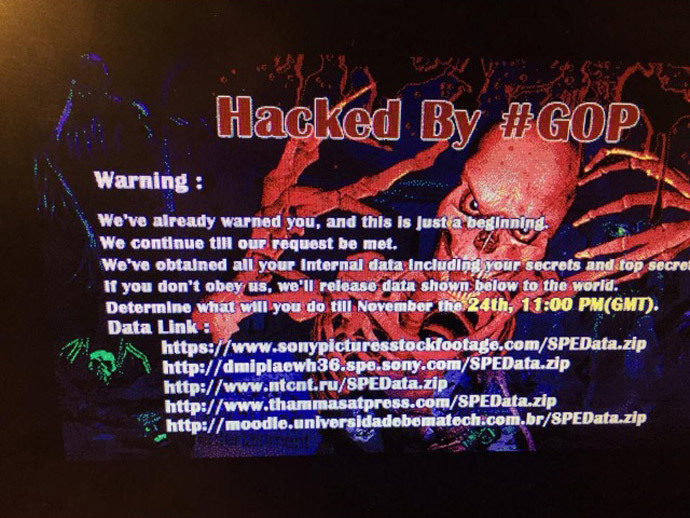
The leak will likely further damage morale at the $8-billion-a-year studio, which has been forced to completely shut down its computer system, since a picture of a blood-red skeleton with the words 'Hacked by #GOP' appeared on employees' monitors on November 24. Work has ground to a halt at the Sony subsidiary, as employees have been forced to use paper and fax for all communications.
Previous leaks have also included salary details and employment reviews of all the company's staff, as well as their criminal and medical records, creating internal tension and external embarrassment for the struggling behemoth. Additionally, the data parcels – which have quickly become available on public torrents – contain its catalogue of upcoming releases.
The cumulative damage will cost the company – which had been struggling even prior to the paralyzing attack – up to “tens of millions” to clean up, according to Kurt Baumgartner, principal for security research at Kaspersky Lab.
FBI refuses to blame N. Korea
The combination of ideological and financial demands continues to fuel rumors about the origin and purpose of the attack. The FBI released its first official statement about the root of the hack on Tuesday.
"There is no attribution to North Korea at this point,” said Joe Demarest, assistant director with the Federal Bureau of Investigation's cyber division, during a security panel in Washington.

FBI officials said that an investigation was ongoing but no additional information could be given out at this time.
Initially, the media and several security companies ran with the most enticing North Korean narrative for the attack. Pyongyang has publicly objected to the release of 'The Interview' since summer, and added fuel to the fire with a statement congratulating the hackers, while failing to take responsibility.

"The hacking into the SONY Pictures might be a righteous deed of the supporters and sympathizers with the DPRK," said an official statement.
Links were made by security industry stalwarts Kaspersky Lab and Symantec between the round of infiltrations and the DarkSeoul attacks that disabled the computers of South Korea’s leading banks and media bodies last year. Seoul blamed its northern neighbor for the cyber onslaught.












