OutlawCountry: ‘CIA hacking tool’ targets Linux operating system (IMAGE)
Published 29 Jun, 2017 17:05 | Updated 29 Mar, 2018 08:24
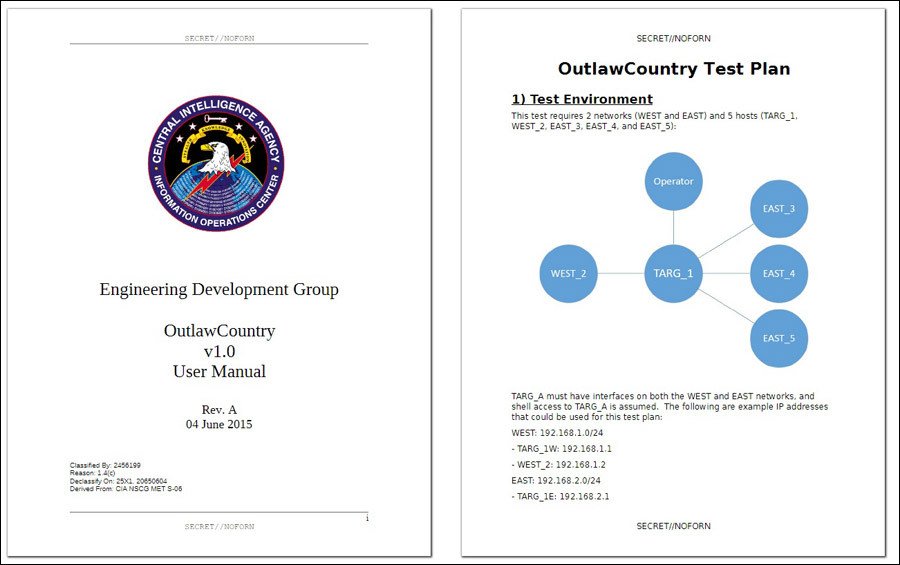
WikiLeaks has published leaked documents purportedly from ‘OutlawCountry’, an alleged CIA program designed to overcome and alter firewalls on a Linux operating device.
An apparent user guide bearing the symbol of the US Central Intelligence Agency was published on the WikiLeaks website Thursday.
RELEASE: #CIA 'Outlaw Country' covert kernel module for #Linuxhttps://t.co/RnNjT8EutT#RHAT#redhat#vault7pic.twitter.com/trdhc4VbJ2
— WikiLeaks (@wikileaks) June 29, 2017
“OutlawCountry allows for the redirection of all outbound network traffic on the target computer to CIA-controlled machines for ex- and infiltration purposes,” WikiLeaks said in a statement.
A type of malware, the virus targets a very specific version of the Linux operating system.
“The target must be running a compatible 64-bit version of CentOS/RHEL 6.x (kernel version 2.6.32),” the program’s user guide says.
READ MORE: CIA can hack & track Windows devices via their wifi connections
The reasons for installing the bug are not explained in the OutlawCountry engineering guide, other than it gives users the opportunity to alter a computer’s security settings.
OutlawCountry is made up of a file that creates a “hidden netfilter table” or new set of firewall settings, the user manual states.
“With knowledge of the table name, an operator can create rules that take precedence over existing netfilter/iptables rules,” the document reads.
All evidence of the virus is destroyed when the netfilter table is removed by the operator.
Red Hat, a provider of Linux open source software, told RT.com that its security team has “crafted a knowledgebase article about OutlawCountry.”
“The article explains that this is not a vulnerability in any Red Hat product. The manual outlines the details of a tool that can be used once an attacker already has local and root access to a system,” a Red Hat spokesperson said.
The article, which appears on the Red Hat website, advises people using a Linux system that has been targeted by the exploit to upgrade to a newer version. A guide on how to manually upgrade can be found here.












