#Vault7: ‘CIA malware plants Gremlins’ on Microsoft machines – WikiLeaks
Published 12 May, 2017 09:47 | Updated 16 Apr, 2018 15:13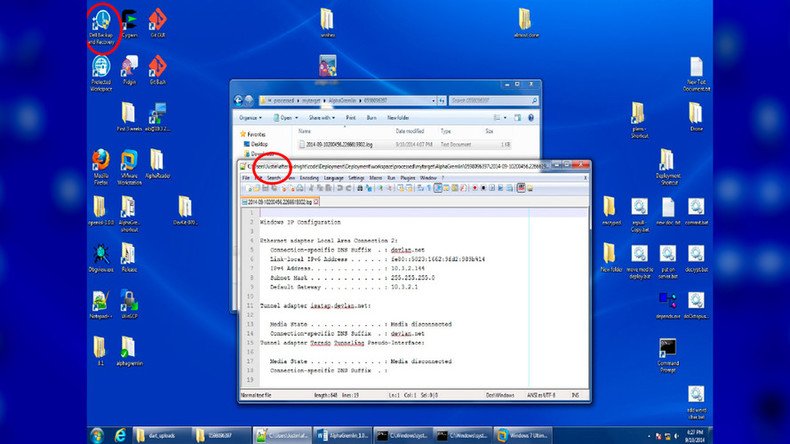
WikiLeaks has released the latest instalment in the #Vault7 series, detailing two apparent CIA malware frameworks dubbed ‘AfterMidnight’ and ‘Assassin’ which it says target the Microsoft Windows platform.
READ MORE: #Vault7: WikiLeaks reveals CIA ‘Scribbles’ tool can track whistleblowers & foreign spies
The latest release consists of five documents detailing the two frameworks. ‘AfterMidnight’ allows operators to load and execute malware on a target machine, according to a statement from WikiLeaks.
The malware, disguised as a self-persisting dynamic-link library (DLL), unique to Microsoft, executes ‘Gremlins’ – small payloads which run hidden on the machine subverting the functionality of software as well as surveying the target and exfiltration of data. A payload named ‘AlphaGremlin’ allows operators to schedule customs tasks to be executed on the machine.
'AfterMidnight' operation, detailed in latest @wikileaks#Vault7 release https://t.co/M2BwsaKzLApic.twitter.com/Hglqdyt5Dy
— Colm McGlinchey (@ColmMcGlinchey) May 12, 2017
Once installed ‘AfterMidnight’ uses a HTTPS listening port to check for any scheduled events. Local storage related to ‘AfterMidnight’ is encrypted with a key not stored on the target machine, according to a user guide provided in the leak.
According to the leak, ‘Assassin’ is a similar type of malware to ‘AfterMidnight’. The tool’s user guide describes it as "an automated implant that provides a simple collection platform on remote computers running the Microsoft Windows operating system.”
The tool purportedly allows operators to perform specific tasks on an infected computer, periodically sending intercepted information to listening posts. It is made up of four subsystems: 'Implant', 'Builder', 'Command and Control', and 'Listening Post'.
The ‘Implant’ provides the core logic and functionality of the tool on a target computer. The way it’s set up determines much of how the tool will behave on the target computer.
The ‘Builder’ arranges the Implant and ‘Deployment Executables’ before deployment, while the ‘Command and Control’ subsystem acts as an interface between the operator and the ‘Listening Post.’
The ‘Listening Post’ allows the ‘Implant’ to communicate with the subsystem through a web server.
Details of the document’s author are revealed in instructional screenshots of their desktop which appear in the ‘AlphaGremlin’ user guide. The screenshots also show a shortcut to Pidgin, an encrypted chat program, along with a folder named ‘Drone.’
Screehgrab from latest #Vault7 release shows author is named 'Justin' and is using a #Dell machine #WikiLeakspic.twitter.com/XYMiN5SDl7
— Colm McGlinchey (@ColmMcGlinchey) May 12, 2017











