Archimedes: WikiLeaks drops latest #Vault7 batch detailing network hacking tool
Published 5 May, 2017 10:15 | Updated 5 May, 2017 10:59
A user manual describing an alleged CIA tool known as ‘Archimedes’, purportedly used to attack computers inside a Local Area Network (LAN), has been released by WikiLeaks. The latest batch is the seventh in the whistleblowing organization’s ‘Vault 7’ series.
RELEASE: CIA '#Archimedes' system for exfiltration and browser hijacking. Includes manuals and binary signatures. https://t.co/XWr33GMGDNpic.twitter.com/TEyhABJvbO
— WikiLeaks (@wikileaks) May 5, 2017
The Archimedes tool enables traffic from one computer inside the LAN to be redirected through a computer infected with this malware and controlled by the CIA, according to WikiLeaks.
READ MORE: #Vault7: Key revelations from WikiLeaks’ release of CIA hacking tools
The technique is used to redirect the target’s computer web browser to an exploitation server while appearing as a normal browsing session, the whistleblowing site said. In this way, the hackers gain an entry point that allows them access to other machines on that network.
The tool's user guide, which is dated December 2012, explains that it’s used to re-direct traffic in a Local Area network (LAN) from a "target's computer through an attacker controlled computer before it is passed to the gateway.”
This allows it to insert a false web-server response that redirects the target's web browser to a server that will exploit their system all the while appearing as if it’s a normal browsing session.
40 targets in 16 countries: Scale of CIA-linked #Vault7 hacking tools revealed by Symantec https://t.co/2IuixxyIhRpic.twitter.com/528zlN0eae
— RT (@RT_com) April 10, 2017
The target of the attack is directed to a webpage that looks exactly like the original page they were expecting to be served, but which contains malware. It’s only possible to detect the attack by examining the page source.
Archimedes is an update to a tool called ‘Fulcrum’ and it offers several improvements on the previous system, including providing a method of "gracefully shutting down the tool on demand.”
An addendum from January 2014 shows that Archimedes was updated to support the ability to run on targets with multiple gateways, i.e. devices used to connect different networks.
READ MORE: ‘Intelligence porn’: FBI director’s new nickname for WikiLeaks
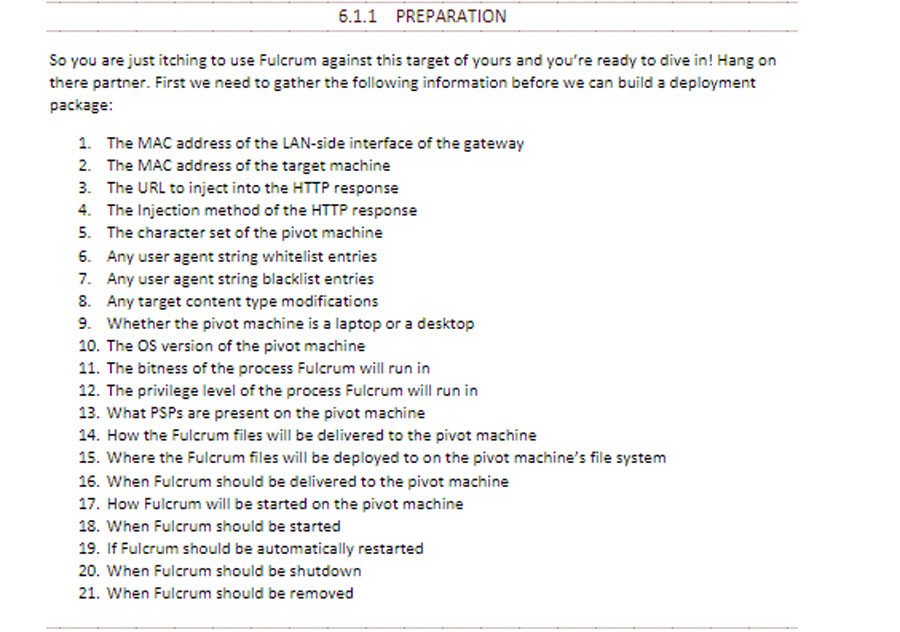
WikiLeaks has also included the Fulcrum user manual in its release, explaining that this tool can direct a target machine’s HTTP client traffic to the URL of the attacker’s choice but specifying it’s not in itself an exploit or a worm.
A worm is a computer program which replicates itself in order to spread malicious code to other computers. Fulcrum will not crash applications or operating systems on the computers it affects, according to the guide.
The guide is dated May 2011 and outlines the entire process from the configuration to the shutdown of the application.
The language used in the Fulcrum user manual is bizarrely casual in contrast to the Archimedes guide.
Describing the steps in packaging applications and configuration data, the Fulcrum guide encourages officials to “Pat yourself on the back, grab a fresh caffeinated beverage of your choice and then let’s get down to it.”
Another section on preparing to use the tool opens: “So you are just itching to use Fulcrum against this target of yours and you’re ready to dive in!”