NSA, GCHQ scour Angry Birds, phone apps for compromising info on users
Published 27 Jan, 2014 21:18 | Updated 29 Jan, 2014 15:00
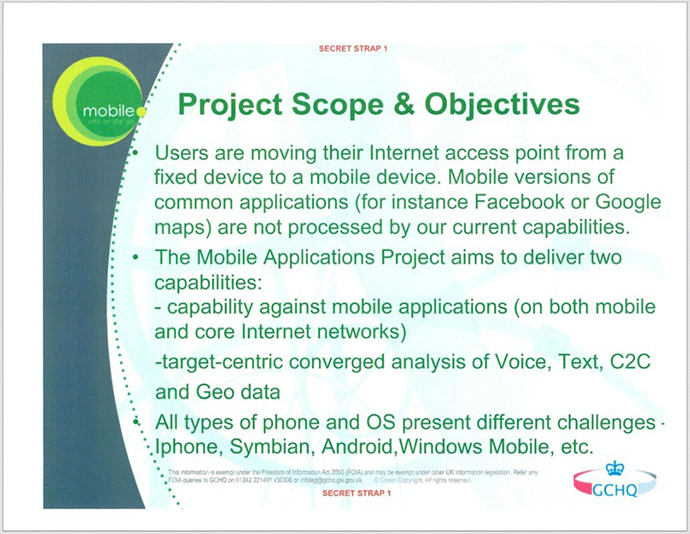
The US National Security Agency and its UK counterpart, GCHQ, have the ability to harvest sensitive personal data from phone apps that transmit users’ data across the web, such as the extremely popular Angry Birds game.
Along with obtaining information about the specific dimensions and model of an individual’s iPhone or Android, the intelligence agencies are also able to acquire details on that person’s age, gender, and location. Details about a user’s political affiliation, sexual orientation, and how promiscuous they are may also be vulnerable.
This information – which was revealed in dozens of top secret documents provided by NSA whistleblower Edward Snowden – was first reported Monday by the Guardian in partnership with the New York Times and ProPublica.
Both the NSA and GCHQ are able to “piggyback” on third party advertisements that a user unwittingly brings onto their device when they first download an app. Those ads, along with geolocation information embedded in images a user uploads to a social media site like Facebook and Twitter, essentially pinpoints where an individual is in the world.
The slides published Monday by the Guardian also show that the intelligence behemoths can glean a person’s home country, current location, age, gender, zip code, marital status – with “single,” “married,” “divorced,” “swinger,” and more among the options – income, ethnicity, sexual orientation, education level, and number of children.
A more sophisticated effort collects location information by intercepting Google map queries from smartphones. It was deemed to be so successful that GCHQ noted in a 2008 document that it “effectively means that anyone using Google maps on a smartphone is working in support of a GCHQ system.”
Scooping up data from apps allows the agencies to gather large quantities of mobile phone data from their existing mass surveillance tools rather than hacking into individual mobile handsets.

Tapping into phone information is a high priority effort for the agencies, as terrorists and other intelligence targets often use mobile phones to plan illegal activities.
One effort by GCHQ and the NSA consists of a database that
geolocates every mobile phone mast in the world. This allows the
agencies to gather the mast ID used with any handset, thus giving
them a rough location for a particular phone.
The latest disclosures add to the public’s concern about how spy
agencies and the technology sector use information, particularly
outside the US where people have fewer privacy protections than
Americans. However, the NSA says it only deploys its capabilities
against “valid foreign intelligence agencies” and does
not target Americans.
The Washington Post reported in December that the NSA was making
use of ‘cookies’ – an online tool which allows internet
advertisers to track consumers. The report said that cookies,
along with location data, were being used by the agency
to“pinpoint targets for government hacking” and “bolster
surveillance.”
Although cookies provide much vaguer information than what is
available through phone apps, a 2010 GCHQ document reveals that
they have become extremely important to intelligence agencies.
But it’s the actual phone handset that remains of paramount
importance. GCHQ’s tools against smartphones are named after
characters in ‘The Smurfs’ cartoon. The ability to make a phone’s
microphone ‘hot’ – in order to listen to conversations – is known
as “Nosey Smurf.” The sophisticated geolocation ability is called
“Tracker Smurf.” Power management – the ability to activate a
phone that is turned off – is known as “Dreamy Smurf.” The
spyware’s self-hiding capabilities are called “Paranoid Smurf.”
















