'Heartbleed' hacking spree: Canadian tax agency says hundreds of IDs stolen
Published 15 Apr, 2014 15:14 | Updated 15 Apr, 2014 15:11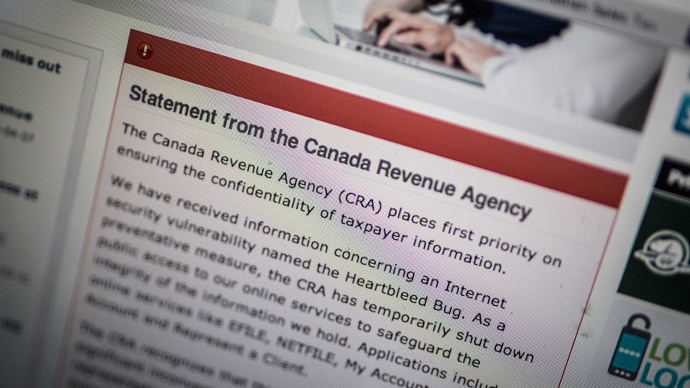
Canada Revenue Agency (CRA) has reported that the private information of about 900 people was stolen using the Heartbleed security bug. Experts are warning that more attacks may occur.
“Based on our analysis to date, Social Insurance Numbers (SIN) of approximately 900 taxpayers were removed from CRA systems by someone exploiting the Heartbleed vulnerability,” the Canadian tax-collection authority said in a statement on Monday. “We are currently going through the painstaking process of analyzing other fragments of data, some that may relate to businesses that were also removed.”
Reportedly, the CRA has so far been the only government agency to admit the data loss after news about the Heartbleed bug became public. The flaw was found in OpenSSL software used to encrypt about two-thirds of websites to secure data. Revealed to the public on Monday, April 7, the bug was feared to be one of the most serious security vulnerabilities in years.
The CRA shut its online services for several days last Tuesday. Unfortunately, it appeared the measure was too slow to prevent attacks by cyber criminals.
“Regrettably, the CRA has been notified by the Government of Canada's lead security agencies of a malicious breach of taxpayer data that occurred over a six-hour period,” the authority said.
The agency, according to its statement, informed the Privacy Commissioner of Canada of the breach on Friday and restored access to its online services on Sunday. However, it waited till Monday to publically confirm the attack.
The CRA “contacted our office last Friday afternoon to notify us about the attack and of the measures it was taking to mitigate risks and notify affected individuals," Valerie Lawton, a spokesperson for the Privacy Commissioner's Office said in a written statement, as cited by CBC News. The office latter added that the tax-collector said that “several hundred Canadians” had their SINs stolen from the agency's website as a result of the Heartbleed bug.
The incident also raised questions over the government’s response to the incident, with researchers in the Canadian online security community saying that the Heartbleed breach indicated that state agencies are often not as well equipped as private firms to react to online threats.
The government “was really slow on this,” Christopher Parsons, from the Citizen Lab at the Munk School of Global Affairs at the University of Toronto told CBC.
“If you look at Yahoo, it had begun updating its security practices prior to the CRA fully taking action. The same thing with other larger companies. As soon as they saw what was going on, they immediately reacted and issued public statements,” he said.
The CRA said in their Monday statement that all those affected by the breach will receive registered letters as well as get access to credit protection services at no cost.
“We will apply additional protections to their CRA accounts
to prevent any unauthorized activity,” the authority said.
Meanwhile, a popular British website for parents, Mumsnet, urged
users to change their passwords after the 'Heartbleed bug' had
been used to access data from their accounts.
“On Thursday April 10 we at MNHQ became aware of the bug and immediately ran tests to see if the Mumsnet servers were vulnerable. As soon as it became apparent that we were, we applied the fix to close the OpenSSL security hole (known as the Heartbleed patch). However, it seems that users' data was accessed prior to our applying this fix,” Mumsnet said.
The founder of the site, Justine Roberts, told the BBC that her own username and password were used to post a message online. According to Roberts, the hackers then told the website’s administrators that the attack was linked to Heartbleed and that the company’s data was not safe.
It is not yet clear why the cyber criminals picked the parental website as their target, as it does not deal with financial or confidential data. But as FT.com noted, people often use same passwords and user names on various websites and hackers may have sought to get those details to use on other sites later.











