Hackers may target brain signals through EEG headsets to access passwords – study
Published 30 Jun, 2017 23:28 | Updated 1 Jul, 2017 11:26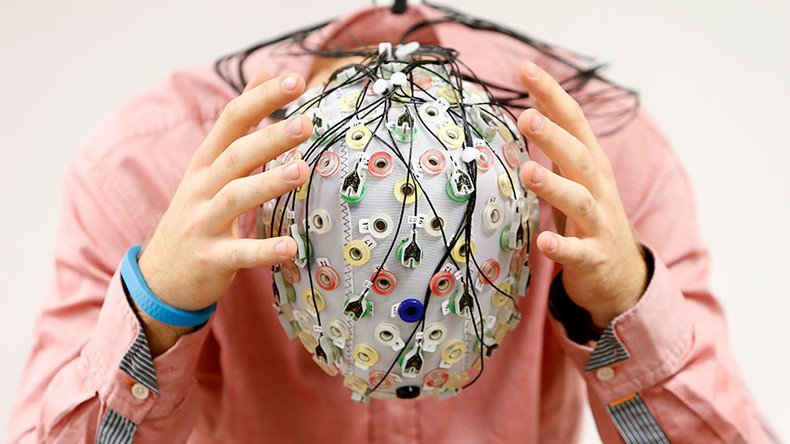
Electronic devices that harness the power of brain signals are one of the latest additions to the world of gaming. A new study has found, however, that hackers could also use such technology to access private information such as passwords and ATM pin codes.
A study by researchers at the University of Alabama at Birmingham has provided an example of how devices that operate using brain signal monitoring, like electroencephalography (EEG), may be a future tool for cyber thieves.
READ MORE: Brain makes decisions before consciousness steps in – leading neuroscientist
Using two EEG headsets, one clinical and the other a commercial product available to consumers, lead researcher professor Nitesh Saxena was able to devise a way to eavesdrop on people’s neural signals.
The study details an attack strategy known as PEEP, described as an advanced type of keylogging, where hackers surreptitiously record via a virus, or determine through sound analysis, strokes on a keyboard.
UAB - News - Study finds hackers could use brainwaves to steal passwords https://t.co/JvicYaHc9U
— Nitesh Saxena (@saxenaUAB) June 28, 2017
Giving an example based in the gaming industry, the “Passively Eavesdropping Private Input” study explains how a hacker could trick a person to download a scam app on their EEG device that would monitor their brain signals.
The malicious app might also ask them to enter a number of numerical values while wearing the headset.
“The developer can claim such codes will secure the game from being played by other users who has access to the computer,” the study states. “The attacker can then process the numeric/alphabetical code and neural signals corresponding to them to extract features.”
By matching brain signals with the values inputted, the researchers indicated that numerical or alphabetical characters could be determined via an algorithm. The study suggests that the odds of guessing a four-digit pin could be shortened to one in 20 rather than one in 10,000.
“In a real-world attack, a hacker could facilitate the training step required for the malicious program to be most accurate, by requesting that the user enter a predefined set of numbers to restart the game after pausing it to take a break, similar to the way the CAPTCHA is used to verify users when logging onto website,” Saxena said.
“Given the growing popularity of EEG headsets and the variety of ways in which they could be used, it is inevitable that they will become part of our daily lives,” Saxena added.
“It is important to analyze the potential security and privacy risks associated with this emerging technology to raise users’ awareness of the risks and develop viable solutions to malicious attacks.”










