Cyberattack on German steel mill inflicts serious damage
Published 21 Dec, 2014 02:17 | Updated 21 Dec, 2014 09:20Unknown hackers have inflicted ‘serious damage’ to a German steel mill this year by breaking into internal networks and accessing the main controls of the factory, the German Federal Office for Information Security (BSI) revealed in its annual report.
The report says that the intrusion into the mainframe system caused significant damage to a blast furnace as the attackers managed to manipulate the internal systems and industrial components, causing outages that disrupted the controlled manner of operation.
The BSI’s didn’t mention which plant was targeted nor gave any reference to the time of the attack. The Office did note the “very advanced” capabilities of the hackers.
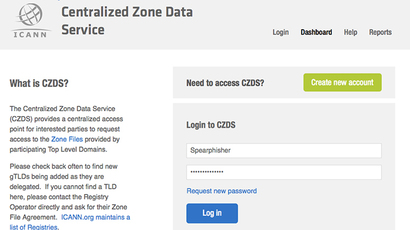
To penetrate the security, the intruders used a “sophisticated spear phishing” method to gain access to the core networks of the plant. Using this method, which involves targeting specific individuals within an organization, the attackers first penetrated the office network of the factory. From there, they managed their way into the production networks.
Benjamin Sonntag, a software developer and digital rights activist told RT that cyber war has been going on for a long time. And while it is nothing new, Sonntag says, the “biggest problem” at the moment is the work of the NSA, “which handle both the defensive approach which is enhancing security of the infrastructure and the offensive approach which is attacking others with mass surveillance.”
READ MORE: Stuxnet patient zero: Kaspesky Lab identifies worm’s first victims in Iran
The steel mill incident, Sonntag says, reminds him of the most famous attack on industrial control systems – Stuxnet. The trojan attack, which was first uncovered in June 2010 was allegedly used by the US and Israel to penetrate a number of Iranian facilities, most notably the Natanz uranium enrichment plant. Stuxnet was responsible for destroyed hundreds of the Iranians’ centrifuges.
“The people who do these kinds of attacks are usually either paid by the state, or mafia, or a big company,” he said. “We do not expect a nuclear power plant or steel plant to be connected to the Internet. To be computerized, but to be connected to the Internet and to be hackable that was is quite unexpected.”
Sonntag says the best way to insure the “safety” of information systems is to make attacks “public and transparent,” so the electronic community can react and protect itself against these types of threats.