Cyber espionage predicted to worsen in 2015 – security experts
Published 9 Dec, 2014 15:54 | Updated 9 Dec, 2014 15:54
With hackers becoming increasingly proficient at their trade, a number of entities – from healthcare industries to average homeowners – will be more vulnerable to invasions of privacy in the coming year.
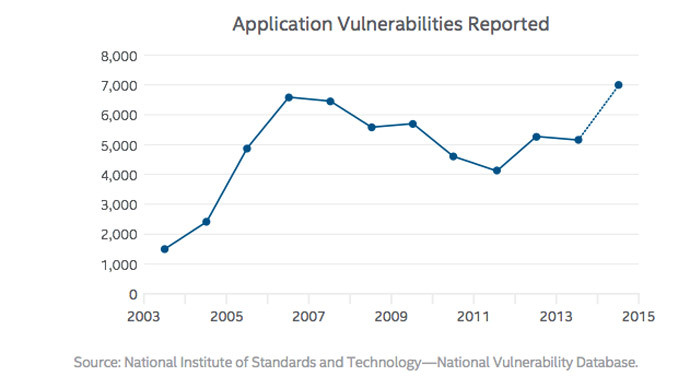
Next year, hackers will be better equipped to launch “crippling distributed denial of service attacks” on unsuspecting users, while, at the same time, employing “sophisticated stealth technologies” to remain below the radar of malware hunters, according to a sobering 2015 Threats Predictions by McAfee Labs' researchers.
The field of players looking to break into computer systems range from common thieves, looking for vulnerable systems to empty a bank account or steal credit card information, to individuals engaged in cyber espionage, aiming to acquire sensitive data from companies and countries.
"In this way, criminals are beginning to look and act more like sophisticated nation-state cyber espionage actors, who watch and wait to gather intelligence," the report said.
The report paid special attention to the health care industry as an especially vulnerable area.
"With the increasing proliferation of healthcare IoT devices and their use in hospitals, the threat of the loss of information contained on those devices becomes increasingly likely," the report said.
READ MORE: Russian cybergang accused of
accumulating most stolen web credentials ever
Medical data "is even more valuable than credit card data" it revealed, quoting information from Reuters. Stolen medical information can go for $10 each, “which is about 10 to 20 times the value of a US credit card number.”
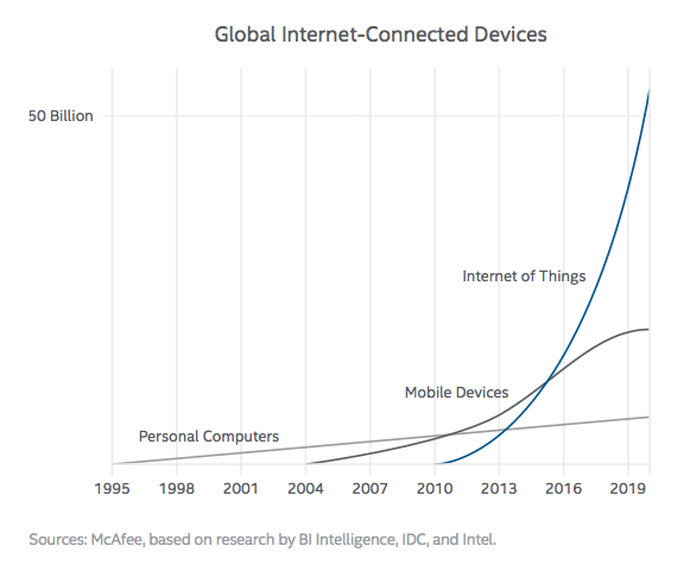
In a particularly worrying quote from the report, McAfee predicts “a major attack” directly connected to vulnerabilities in Internet of Things (IoT) devices, which include “appliances, automobiles, home automation, and even light bulbs.”
“What was once the realm of nation states and enterprising cybercrime organizations can now become the playground of any motivated attacker. We predict that there will be a major attack in 2015 directly related to vulnerabilities in IoT devices,” the report warned.
On the extreme end of the hacker spectrum are those individuals who would carry out attacks that could potentially cripple any computer-linked item - from an automobile to a nuclear power station.
The report warned of an uptick in the number of small nations and terror organizations attempting to "attack by launching crippling distributed denial of service attacks or using malware that wipes the master boot record to destroy their enemies' networks."
Closer to home, hackers will expand their expertise on so-called “ransomware,” which blocks victims from accessing files until they agree to pay a ransom to recover it. This may also include ransoms demanded on photographs and videos accessed from mobile phones.
In September, a sensational scandal erupted as leaked nude photos of more than 100 celebrities landed on the internet.
McAfee researchers mentioned a conference last year where researchers demonstrated how some internet-connected security video cameras could be easily targeted, allowing hackers to access the video feed.
READ MORE: Home Depot confirms data breach, hit
by same malware as Target
Such a breach could prove particularly dangerous to homeowners, who leave their residences for long periods of time.
Another area of concern involves keeping credit card information protected during online purchases. In November, for example, Home Depot estimated 56 million customer credit cards were breached, with losses from the intrusion hitting almost $3 billion.
"With consumers now sending payment information over a protocol with known vulnerabilities, it is highly likely that attacks on this infrastructure will emerge in 2015," the report said.
These events combined have taken a heavy toll on the trust of consumers, the report said.
"2014 will be remembered as the year of shaken trust," said Vincent Weafer, senior vice president at McAfee.
"Restoring trust in 2015 will require stronger industry collaboration, new standards for a new threat landscape, and new security postures that shrink time-to-detection."